- About Apple threat notifications and protecting against state-sponsored attacks
- Apple Outlines How It Will Notify Users Who Have Been Targeted by State-Sponsored Spyware Attacks
- What to do before you sell, give away, or trade in your Mac
- Should you use these steps?
- Back up or transfer your files
- Sign out of iTunes
- Sign out of iCloud
- Sign out of iMessage
- Reset NVRAM
- Optional: Unpair Bluetooth devices that you’re keeping
- Erase your Mac and reinstall macOS
- Pastila: Master an apple treat that once delighted the tsars
- Ingredients:
- Cooking:
About Apple threat notifications and protecting against state-sponsored attacks
Apple threat notifications are designed to inform and assist users who may have been targeted by state-sponsored attackers.
Apple threat notifications are designed to inform and assist users who may have been targeted by state-sponsored attackers. These users are individually targeted because of who they are or what they do. Unlike traditional cybercriminals, state-sponsored attackers apply exceptional resources to target a very small number of specific individuals and their devices, which makes these attacks much harder to detect and prevent. State-sponsored attacks are highly complex, cost millions of dollars to develop, and often have a short shelf life. The vast majority of users will never be targeted by such attacks.
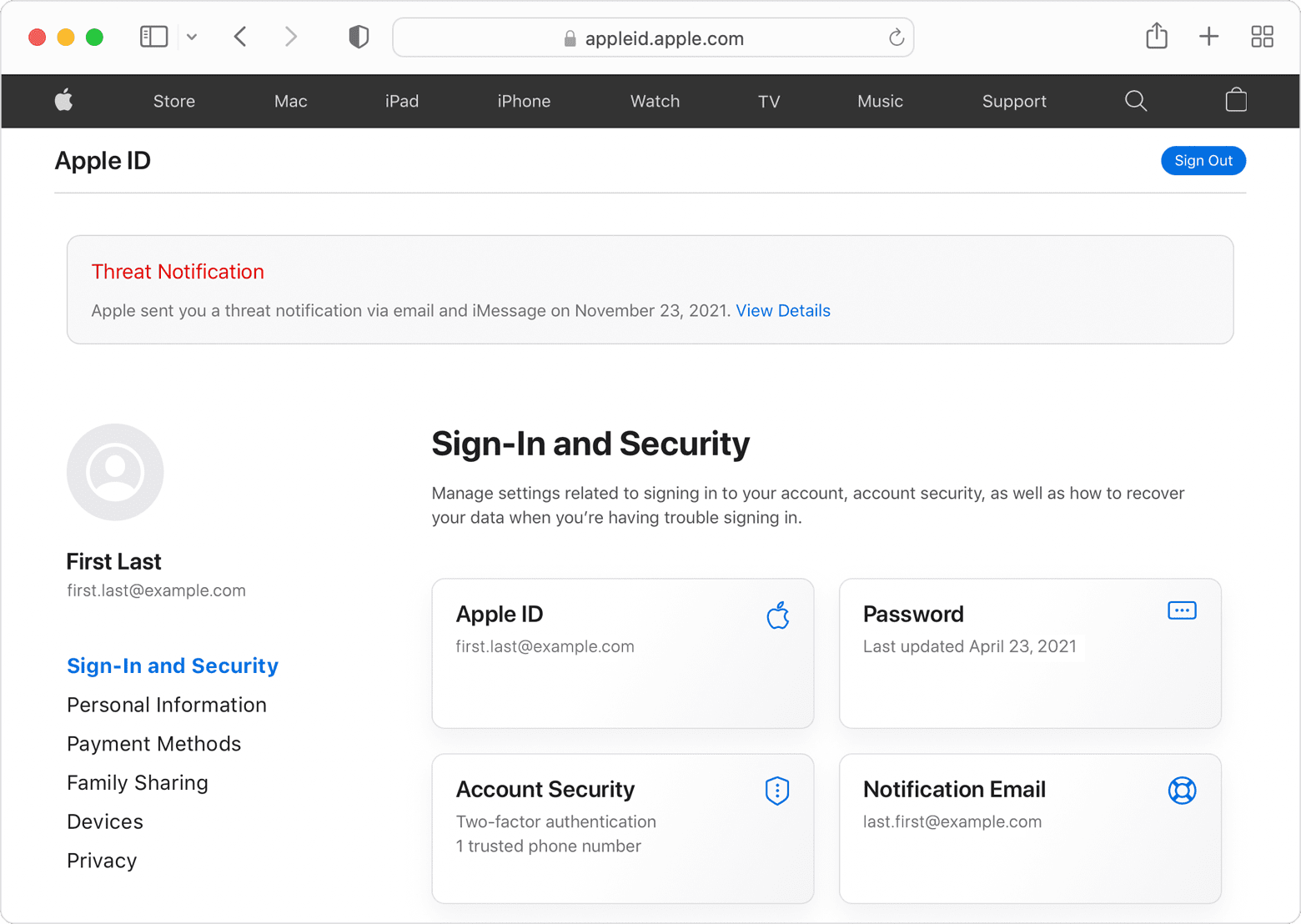
If Apple discovers activity consistent with a state-sponsored attack, we notify the targeted users in two ways:
- A Threat Notification is displayed at the top of the page after the user signs into appleid.apple.com.
- Apple sends an email and iMessage notification to the email addresses and phone numbers associated with the user’s Apple ID.
These notifications provide additional steps that notified users can take to help protect their devices.
State-sponsored attackers are very well-funded and sophisticated, and their attacks evolve over time. Detecting such attacks relies on threat intelligence signals that are often imperfect and incomplete. It’s possible that some Apple threat notifications may be false alarms, or that some attacks are not detected. We are unable to provide information about what causes us to issue threat notifications, as that may help state-sponsored attackers adapt their behavior to evade detection in the future.
Apple threat notifications will never ask you to click any links, open files, install apps or profiles, or provide your Apple ID password or verification code by email or on the phone. To verify that an Apple threat notification is genuine, sign in to appleid.apple.com. If Apple sent you a threat notification, it will be clearly visible at the top of the page after you sign in.
All users should continue to protect themselves from cybercriminals and consumer malware by following best practices for security:
- Update devices to the latest software, as that includes the latest security fixes
- Protect devices with a passcode
- Use two-factor authentication and a strong password for Apple ID
- Install apps from the App Store
- Use strong and unique passwords online
- Don’t click on links or attachments from unknown senders
If you have not received an Apple threat notification, but have good reason to believe you may be targeted by state-sponsored attackers or you require emergency cybersecurity assistance for other reasons, we strongly suggest you enlist expert help. The Consumer Reports Security Planner website offers a list of emergency resources that may be able to assist you.
Information about products not manufactured by Apple, or independent websites not controlled or tested by Apple, is provided without recommendation or endorsement. Apple assumes no responsibility with regard to the selection, performance, or use of third-party websites or products. Apple makes no representations regarding third-party website accuracy or reliability. Contact the vendor for additional information.
Источник
Apple Outlines How It Will Notify Users Who Have Been Targeted by State-Sponsored Spyware Attacks
Earlier today, Apple announced that it had filed suit against NSO Group, the firm responsible for the Pegasus spyware that has been used in state-sponsored surveillance campaigns in a number of countries. NSO Group seeks to take advantage of vulnerabilities in iOS and other platforms to infiltrate the devices of targeted users such as journalists, activists, dissidents, academics, and government officials.
As part of its announcement, Apple revealed that it is notifying the «small number of users» who have been targeted via the FORCEDENTRY exploit for a now-patched vulnerability that allowed Pegasus to be installed on their devices. Apple also said that it will continue to notify users it believes have been targeted by state-sponsored spyware attacks «in accordance with industry best practices,» and the company has now shared a new support document outlining how it will notify those users.
Notifications will be delivered to affected users via email and iMessage notifications to the addresses and phone numbers associated with the users’ Apple IDs, with the notifications providing additional steps users can take to protect their devices. A prominent «Threat Notification» banner will also be displayed at the top of the page when affected users log into their accounts on the Apple ID web portal.
Users will never be asked to click links or install apps via the email and iMessage notifications, so users receiving notifications should always log into their Apple ID accounts on the web to verify that threat notifications have been issued for their accounts and to learn what to do next.
Apple acknowledges that there may be some false alarms with its notifications and that some attacks may go undetected, as it is facing constantly evolving tactics from state-sponsored attackers. Apple’s threat-detection methods will similarly evolve, and so the company will not be sharing information on its methods to hinder efforts by attackers to evade detection.
Regardless of whether or not you receive a threat notification from Apple, the company advises all users to take the following steps to secure their devices:
- Update devices to the latest software, as that includes the latest security fixes
- Protect devices with a passcode
- Use two-factor authentication and a strong password for Apple ID
- Install apps from the App Store
- Use strong and unique passwords online
- Don’t click on links or attachments from unknown senders
Finally, Apple shares a list of emergency resources at the Consumer Reports Security Planner website for those users who have not received an Apple threat notification but believe they may have been targeted by state-sponsored attackers to obtain expert assistance.
Note: Due to the political or social nature of the discussion regarding this topic, the discussion thread is located in our Political News forum. All forum members and site visitors are welcome to read and follow the thread, but posting is limited to forum members with at least 100 posts.
Источник
What to do before you sell, give away, or trade in your Mac
To prepare your Mac for a new owner, use these steps restore it to factory settings.
Should you use these steps?
If you’ve upgraded to macOS Monterey on a Mac with Apple silicon or a Mac with the Apple T2 Security Chip, follow the steps to erase all content and settings instead of the steps in this article.
For any other Mac or macOS, follow the steps below.
Back up or transfer your files
Use an external storage device to back up your files, or use Migration Assistant to move your files to your new Mac.
Sign out of iTunes
If using macOS Catalina or later, you can skip this step.
Open iTunes. From the menu bar at the top of the screen or iTunes window, choose Account > Authorizations > Deauthorize This Computer. Then enter your Apple ID and password and click Deauthorize. Learn more about deauthorizing.
Sign out of iCloud
If using macOS Catalina or later, choose Apple menu > System Preferences, then click Apple ID. Select Overview in the sidebar, then click Sign Out.
If using an earlier version of macOS, choose Apple menu > System Preferences, click iCloud, then click Sign Out.
You will be asked whether to keep a copy of your iCloud data on this Mac. You can keep a copy, because you’re erasing your Mac later. Your iCloud data remains in iCloud and on any other devices that are signed in to iCloud with your Apple ID.
Sign out of iMessage
Open the Messages app, then choose Messages > Preferences from the menu bar. Click iMessage, then click Sign Out.
Reset NVRAM
If using a Mac with Apple silicon, you can skip this step.
Shut down your Mac, then turn it on and immediately press and hold these four keys together: Option, Command, P, and R. Release the keys after about 20 seconds. This clears user settings from memory and restores certain security features that might have been altered. Learn more about resetting NVRAM .
Optional: Unpair Bluetooth devices that you’re keeping
If your Mac is paired with a Bluetooth keyboard, mouse, trackpad, or other device that you plan to keep, you can unpair it. This optional step prevents accidental input when the Mac and device have separate owners but remain in Bluetooth range. If you do this on a Mac that doesn’t have a built-in keyboard or trackpad, you will need to plug in a USB keyboard and mouse to complete the remaining steps.
To unpair a Bluetooth device, choose Apple menu > System Preferences, then click Bluetooth. Move your pointer over the device that you want to unpair, then click the remove (x) button next to the device name.
Erase your Mac and reinstall macOS
Follow the steps to erase your Mac and reinstall macOS. After macOS installation is complete, your Mac restarts to a setup assistant. To leave the Mac in an out-of-box state, press Command-Q to shut down instead of continuing setup.
No matter the model or condition, we can turn your device into something good for you and good for the planet: Learn how to trade in or recycle your Mac with Apple Trade In.
Источник
Pastila: Master an apple treat that once delighted the tsars
By now you’ve probably heard and read about pastila. It is one of the oldest and most traditional Russian sweet delights, and can be compared to a marshmallow. But a real Russian will always argue with you about that, and will never agree to call pastila a marshmallow.
Traditionally, pastila is made from only two to three ingredients and doesn’t contain either starch or gelatin. Pastila is dried several times in a traditional Russian oven, inside special wooden boxes made of alder.
The peculiarity of pastila, as a purely Russian confection, is that it is made from Antonov apples, which can only be found in Russia, and which are especially tangy and aromatic. Every child in Russia is taught that this is the best sort of apple to bake with, whether we are talking about pies, cakes or any type of apple-based desserts.
You will be actually surprised how much history pastila has!
Before the revolution of 1917, pastila was produced in three cities: Kolomna, Rzhev and Belev. Each variety was named after the place of production, and each recipe had its secret ingredients.
The largest production was in Belev, and was founded by the industrialist and merchant, Ambrose Prokhorov, who in 1858 planted a large apple orchard. In 1888 he opened a production with a “drying room” for processing fruit, which began to produce pastila.
In 1890, Belevskaya pastila even won first prize at a gardening exhibition in St. Petersburg, after which Prokhorov opened stores in Moscow, St. Petersburg, Kiev and Tbilisi. Then, for the first time, it was exported as a Russian national confectionary to Western Europe!
Pastila production in Belev was temporarily suspended in 1918 when Prokhorov’s property was nationalized. Later, it was resumed by his son Nikolai, who opened the Prokhorov and Sons brand store in Moscow. In 1926, attempts were made to put production of Belev pastila under state control. Nikolai Prokhorov was offered to become chief engineer of the Belevsk State Drying Factory. After his refusal, he was persecuted by the state.
Nevertheless, the pastila production facility worked until the early 1990s, when it was closed for several years. After that, Belevskaya pastila was produced only by craftsmen. The facility resumed work only in early 2000 and makes pastila according to traditional recipes, which has propelled it to great popularity both at home and abroad.
The process of making pastila is tedious, but trust me, the result is really worth it because pastila is a royal treat fit for the Tsar!
Ingredients:
- 8 apples (acidic varieties)
- 170g sugar
- 1 egg white
- powdered sugar
Cooking:
1. Heat the oven to 180 ℃. Place whole apples on a sheet tray and bake for about 45-60 minutes until very soft. Some apples will burst, but it’s not a problem!
2. Once the apples are baked, blend them with skin and cores until they become a smooth puree. Then pass them through a very fine strainer so the unblended parts get separated. Let the puree cool.
3. In the mixing bowl, measure 500g of apple puree, add the egg white and sugar. Whip this mixture on the highest speed for 5-7 minutes. It should increase in volume and become much lighter in color.
4. Prepare a sheet tray with baking paper. Grease lightly, and place a cup of apple mixture in the fridge. The rest of the mixture spread on the sheet tray about 2cm thick.
5. Heat the oven until 100 ℃ on a convection setting (if you have one). Dry the pastila for about 3-4 hours, opening the oven door every 30 minutes to release excess moisture. The pastila will become a little darker and will settle, but it won’t be sticky anymore.
6. Take out the pastila and let it cool. Carefully turn it upside down on baking paper, removing the baking paper that was on the bottom. Cut the pastila into 3 equal strips.
7. Take the cup of apple mixture from the fridge. Put the dried strips on top of each other with a thin layer of apple mixture; also,cover the sides and the top. Place the pastila back in the oven and dry for about 2 more hours, opening the oven door every 30 minutes.
8. Once your pastila is ready, let it cool completely, and then rub the sides, bottom and the top with powdered sugar. Pastila will stay fresh if you store it in an airtight bag: that is, if you have any leftovers to store.
If using any of Russia Beyond’s content, partly or in full, always provide an active hyperlink to the original material.
to our newsletter!
Get the week’s best stories straight to your inbox
Источник