- Configuring an Android Device to Work With Burp
- Configure the Burp Proxy listener
- Configure your device to use the proxy
- Test the configuration
- Installing Burp’s CA Certificate in an Android Device
- Configuring Burp Suite With Android Nougat
- Table of Contents
- Background
- Install Burp CA as a system-level trusted CA
- Mofiying and repackaging an app
Configuring an Android Device to Work With Burp
To test web applications using an Android device you need to configure your Burp Proxy listener to accept connections on all network interfaces, and then connect both your device and your computer to the same wireless network. If you do not have an existing wireless network that is suitable, you can set up an ad-hoc wireless network.
Configure the Burp Proxy listener
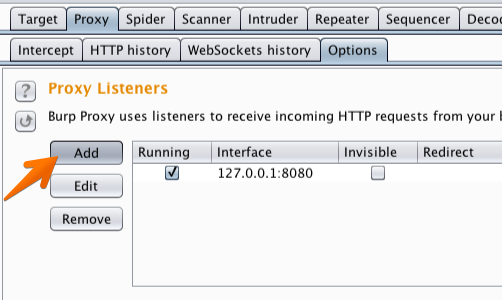
In Burp, go to the “Proxy” tab and then the “Options” tab.
In the “Proxy Listeners» section, click the “Add” button.
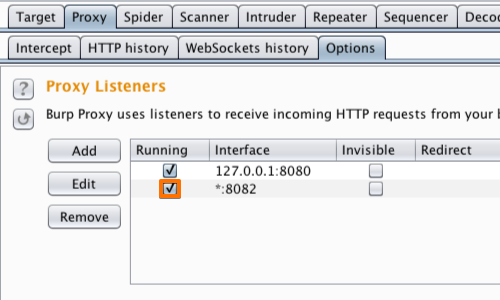
In the «Binding» tab, in the “Bind to port:” box, enter a port number that is not currently in use, e.g. “8082”.
Then select the “All interfaces” option, and click «OK».
Note: You could alternatively edit the existing default proxy listener to listen on all interfaces. However, using different listeners for desktop and mobile devices enables you to filter these in the Proxy history view.
The Proxy listener should now be configured and running.
Configure your device to use the proxy
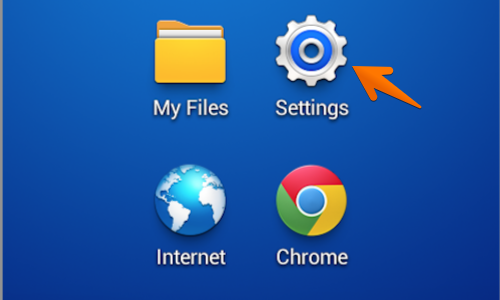
In your Android device, go to the“Settings” menu.
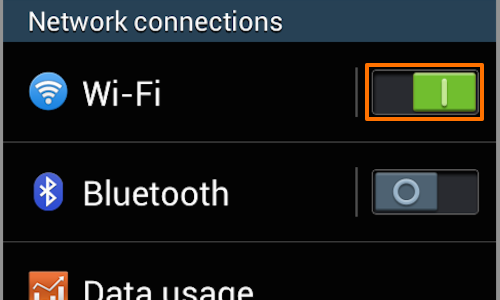
If your device is not already connected to the wireless network you are using, then switch the «Wi-Fi» button on, and tap the “Wi-Fi” button to access the «Wi-Fi» menu.
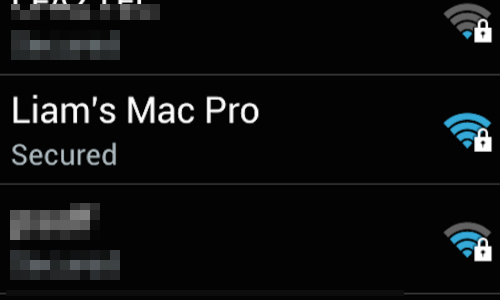
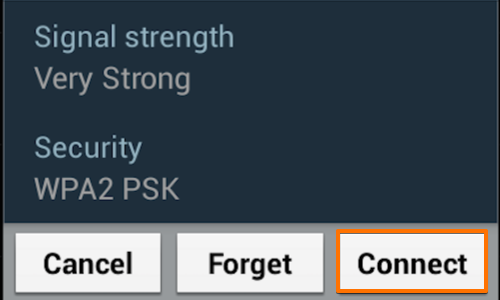
In the «Wi-Fi networks» table, find your network and tap it to bring up the connection menu.
If you have configured a password, enter it and continue.
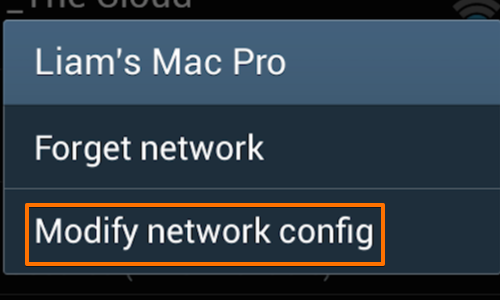
Once you are connected hold down on the network button to bring up the context menu.
Tap “Modify network config”.
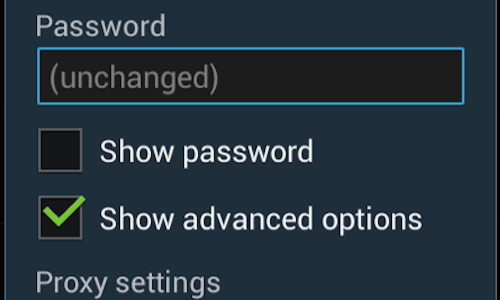
Ensure that the “Show advanced options” box is ticked.
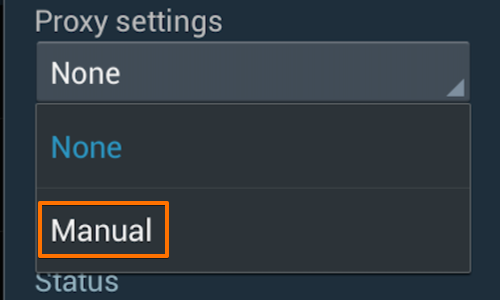
Change the “Proxy settings” to “Manual” by tapping the button.
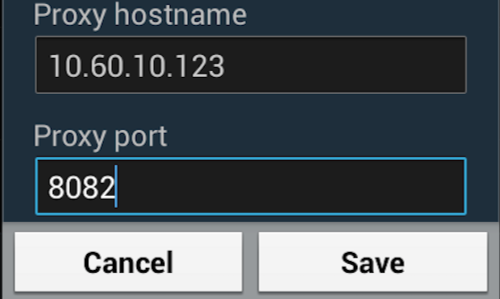
Then enter the IP of the computer running Burp into the “Proxy hostname”.
Enter the port number configured in the “Proxy Listeners” section earlier, in this example “8082”.
Test the configuration
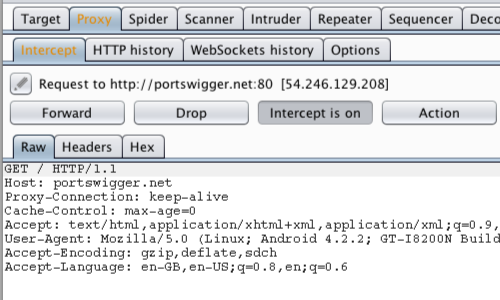
In Burp, go to the «Proxy Intercept» tab, and ensure that intercept is “on” (if the button says “Intercept is off» then click it to toggle the interception status).
Open the browser on your Android device and go to an HTTP web page (you can visit an HTTPS web page when you have installed Burp’s CA Certificate in your Android device.)
The request should be intercepted in Burp.
Note: On some Android emulators you will need to add the proxy details from the emulator settings menu rather than the native Network / Wifi settings on the emulated device.
Источник
Installing Burp’s CA Certificate in an Android Device
Before you start:
- Ensure you have configured your Android device to work with Burp.
- Ensure your Android device is able to receive email, and that your email filter does not block .cer files.
Note: Android Nougat no longer trusts user or admin supplied CA certificates. We recommend that you use an older version of Android for your testing. If you must use Android Nougat then you will need to install a trusted CA at the Android OS level on a rooted device or emulator.
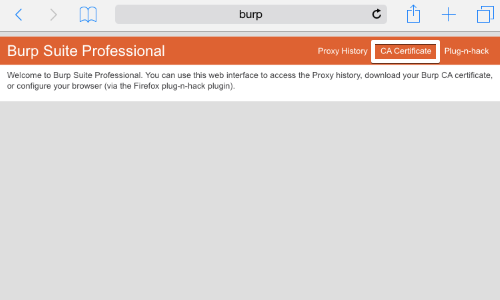
On your computer with Burp running, visit http://burpsuite and click the «CA Certificate» link. Save the certificate file on your computer.
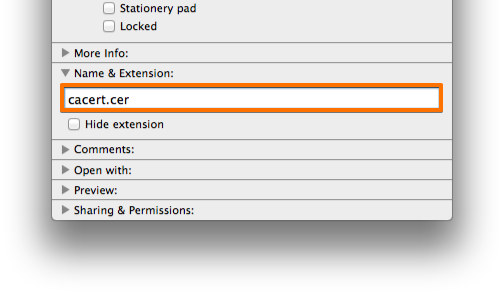
On your computer, rename the file with the .cer file extension, and send the file as an email attachment to an account that you can access from your Android device.
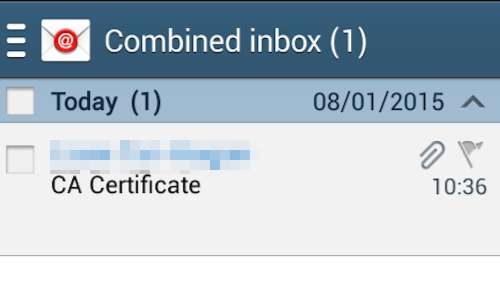
Check your email on the Android device.
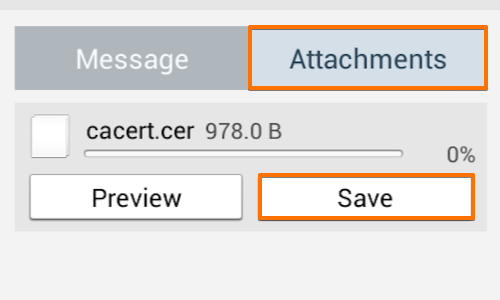
Open the email and tap the attachments button.
Then tap the save button. This should save the certificate file to your Android device’s “Download» folder.
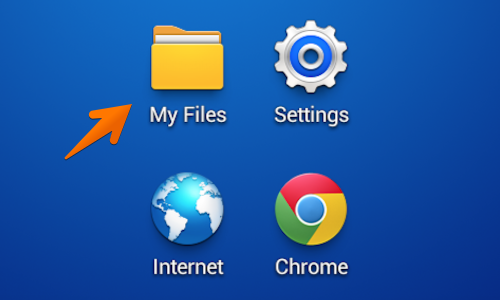
Find your “My Files” folder. This may be located in the “Apps” menu or on one of the device’s home screens.
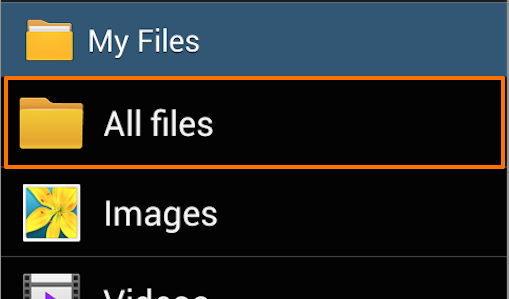
In “My Files” tap the “All Files” folder.
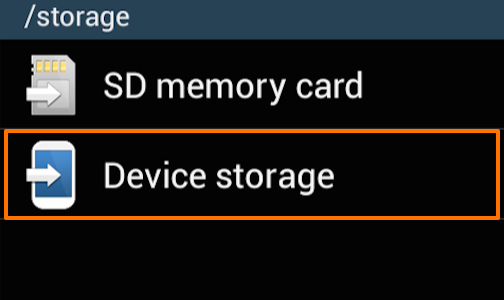
In the “All Files” folder tap “Device storage”.
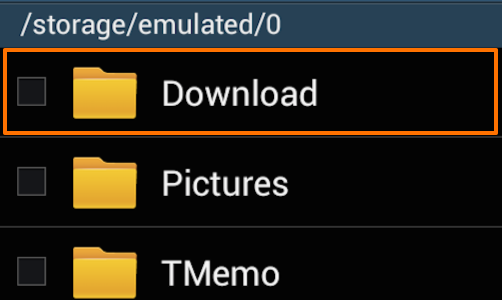
Open the “Download” folder and check that your certificate is correctly located in this folder.
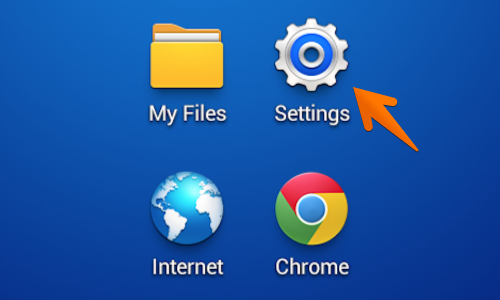
Next locate and tap the «Settings” icon. This may be located in the “Apps” menu or on one of the device’s home screens.
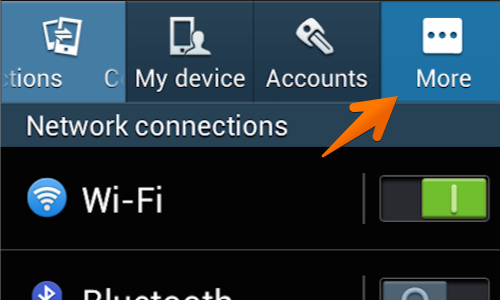
Tap the “More” button.
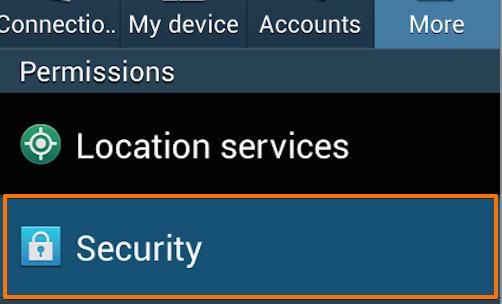
Beneath the “Permissions” header tap the “Security” button.
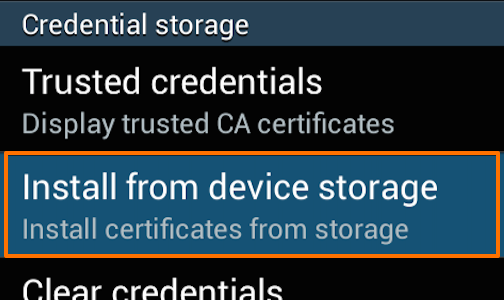
In the “Security” menu select the “Install from device storage” from beneath the «Credential storage» header.
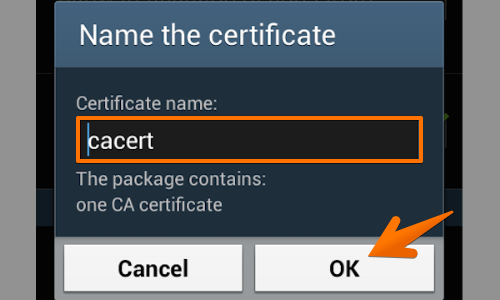
You will now be asked to “Name the certificate”, leave the certificate name as it is and tap “OK”.
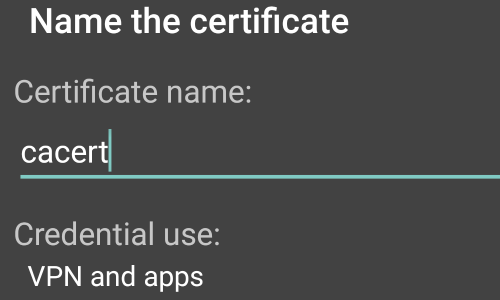
In some versions of Android, your device will ask if you want to use the certificate for «VPN and apps» or «WiFi».
In the «Credential use:» options, you should select «VPN and apps».
The phone will revert to the security menu and will inform you via a small pop up that the certificate is installed.
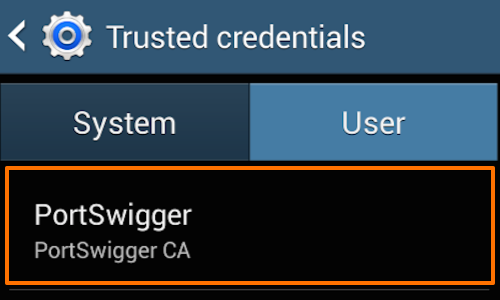
You can check the Certificate is installed by tapping the “Trusted credentials» button.
Tap the «User» tab in the “Trusted credentials” window to show the PortSwigger CA certificate.
You should now be able to visit any HTTPS URL via Burp without any security warnings.
Note: It is also possible to import the Burp CA Certificate using a micro SD card. Ensure that you move the Burp CA Certificate from the micro SD card to the phones own storage before using the certificate install function in the “Security” menu.
This article is based on Android version 4.2.2 running on a Samsung mobile device.
Источник
Configuring Burp Suite With Android Nougat
Table of Contents
This last weekend I started testing a new Android app for fun, and ran into some trouble getting Burp Suite working properly. I burned a whole afternoon troubleshooting the issue, and decided to write up what I found out and two different ways I got it working.
Background
I’ve done quite a bit of Android testing in the past and my setup usually involves a Genymotion VM or my old rooted Nexus Tablet. I run Burp Suite locally, install the User Cert as outlined in Portswigger’s documentation, configure a WiFi proxy and I’m off the races.
This particular app I wanted to test, however, required a minimum API level 24 (Android 7.0 — “Nougat”) and suddenly it wasn’t working. I followed the steps I always do but saw nothing but “connection reset” errors in Burp:
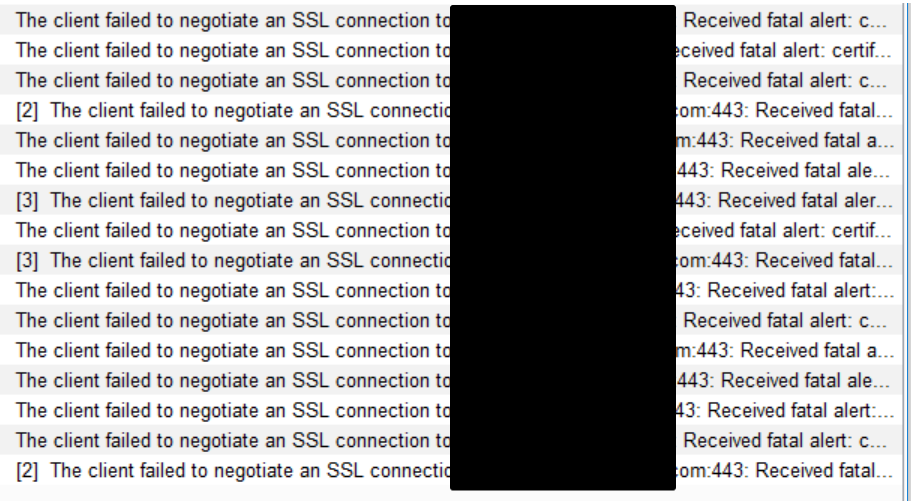
After a few frustrating hours of troubleshooting, I finally figured out the issue lied with the latest versions of Android (API >= 24). Before I go any further, all the information I needed was found in these great write-ups:
Starting with Nougat, Android changed the default behavior of trusting user installed certificates. It’s no longer possible to just install the Burp CA from the sdcard to start intercepting app traffic. Unless otherwise specified, apps will now only trust system level CAs. The failure happens “invisibly” and is responsible for all the alerts I saw in Burp Suite.
There’s two ways to bypass this, and I’ll walk through them both.
- Install the Burp CA as a system-level CA on the device. My recommendation for the easiest solution, but does require a rooted device. Also added benefit of not having to set a lockscreen PIN 🙂
- Modify the manifest and repackage the app. Slightly more work, but doesn’t require root privileges.
Note: I did all this with Burp Suite Pro on my Windows 10 machine and am using an Android 7.1 (API25) Genymotion VM, but the steps should be applicable to any setup.
Install Burp CA as a system-level trusted CA
Since the “traditional” way of installing a user certificate doesn’t work anymore in Nougat and above, for me the easiest solution is to install the Burp CA to the system trusted certificates. You can see all the system CAs that are bundled with an Android device by going to Settings -> Security -> Trusted Credentials and viewing system CAs. You’ll see the similar CAs you’d see in a browser bundle.
Trusted CAs for Android are stored in a special format in /system/etc/security/cacerts . If we have root privileges, it’s possible to write to this location and drop in the Burp CA (after some modification).
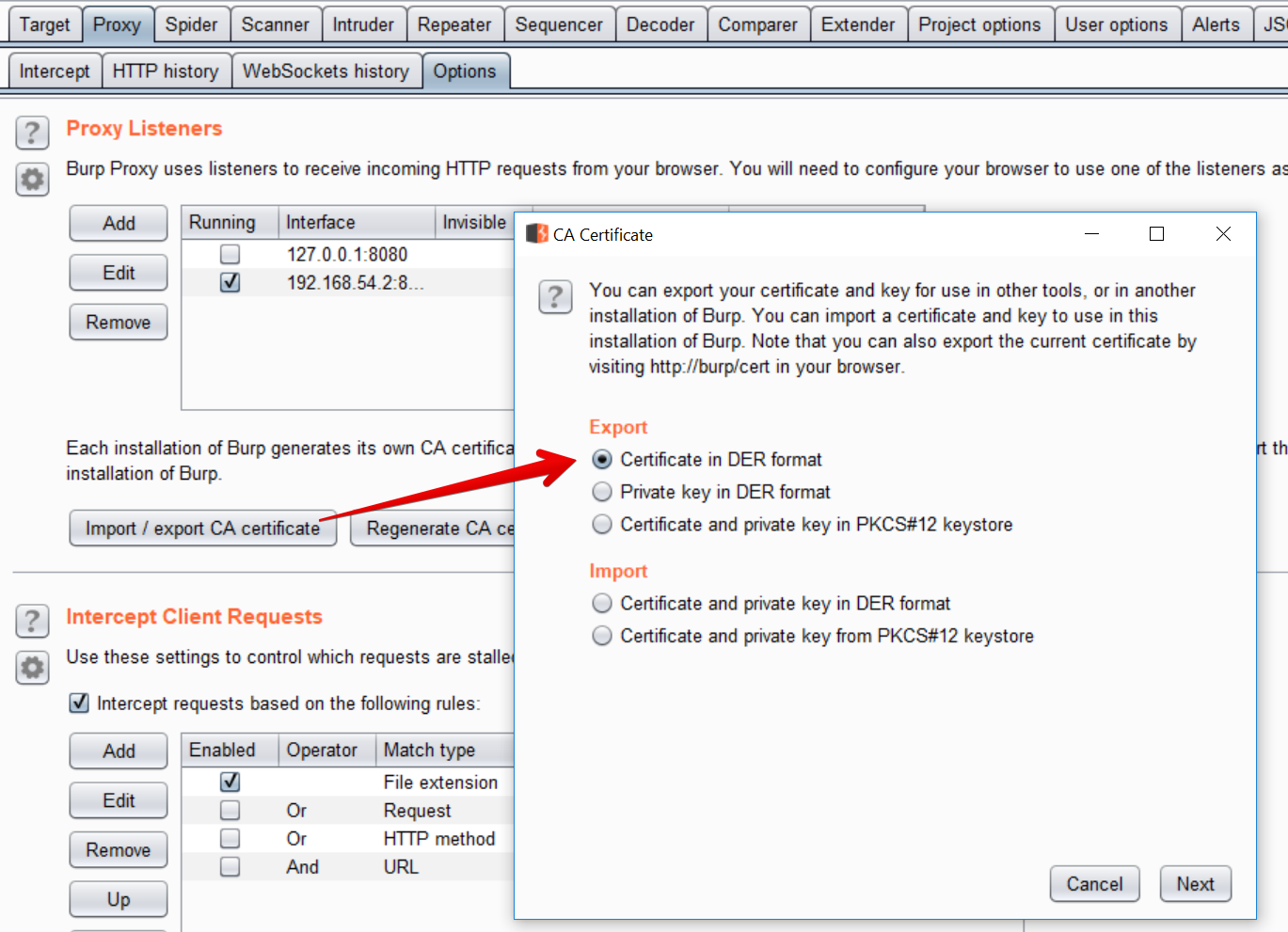
Export and convert the Burp CA The first step is to get the Burp CA in the right format. Using Burp Suite, export the CA Certificate in DER format. I saved it as cacert.der
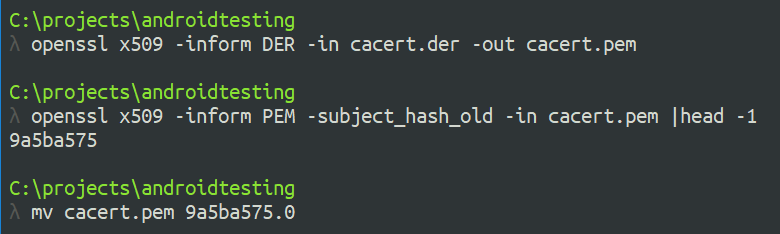
Android wants the certificate to be in PEM format, and to have the filename equal to the subject_hash_old value appended with .0 .
Note: if you are using OpenSSL subject_hash , not the “old” one
Use openssl to convert DER to PEM, then output the subject_hash_old and rename the file:
For example, with my certificate:
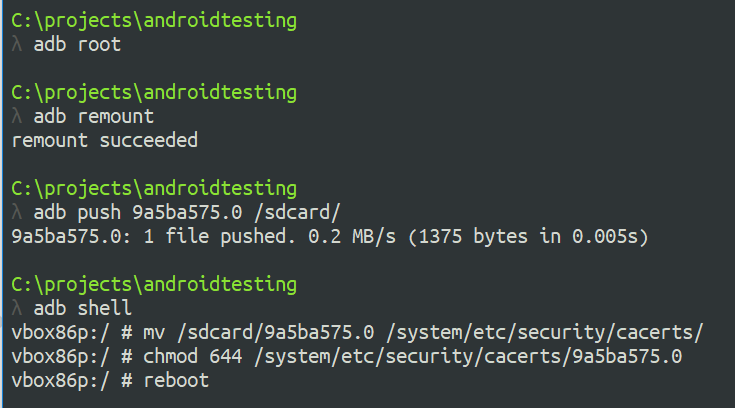
Copy the certificate to the device We can use adb to copy the certificate over, but since it has to be copied to the /system filesystem, we have to remount it as writable. As root, this is easy with adb remount .
The just drop into a shell ( adb shell ) and move the file to /system/etc/security/cacerts and chmod it to 644:
Lastly, we have to full reboot the device with either adb reboot or a power cycle.
After the device reboots, browsing to Settings -> Security -> Trusted Credentials should show the new “Portswigger CA” as a system trusted CA.
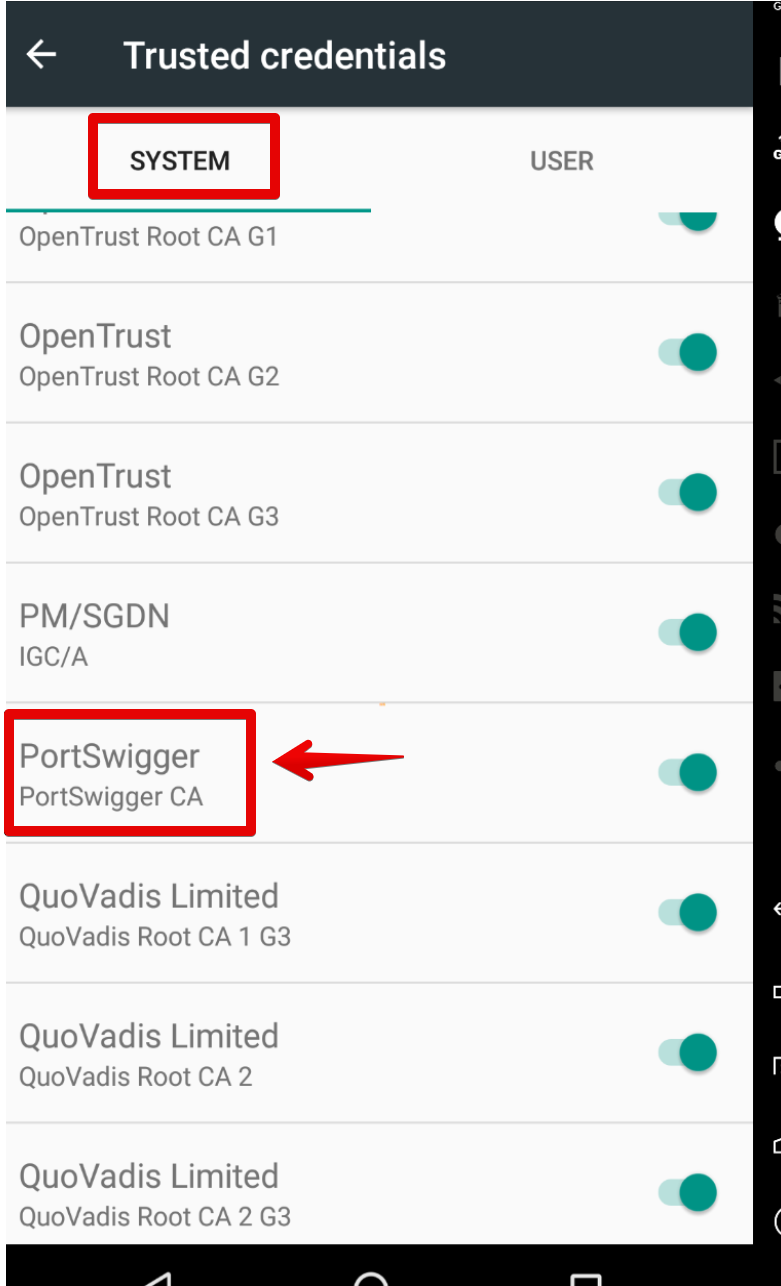
Now it’s possible to set up the proxy and start intecepting any and all app traffic with Burp 🙂
Mofiying and repackaging an app
If you don’t have root or don’t want to modify the system trusted certificates, you can install the Burp CA as a user cert and then modify the specific APK you want to MitM.
Starting with Nougat, apps will ignore user-installed certificates by default. This is evident by looking at logcat output when launching the app:
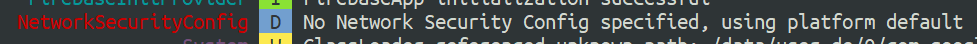
Without a network security config, the app will only trust system CAs and will not honor the user installed Burp certificate.
To get around this, it involves:
- Disassembling the APK
- Adding a new XML resource to define a network security profile
- Modifying AndroidManifest.xml
- Repackaging and self-signing the APK
Disassemble and modify the APK Start by using apktool to disassemble the APK
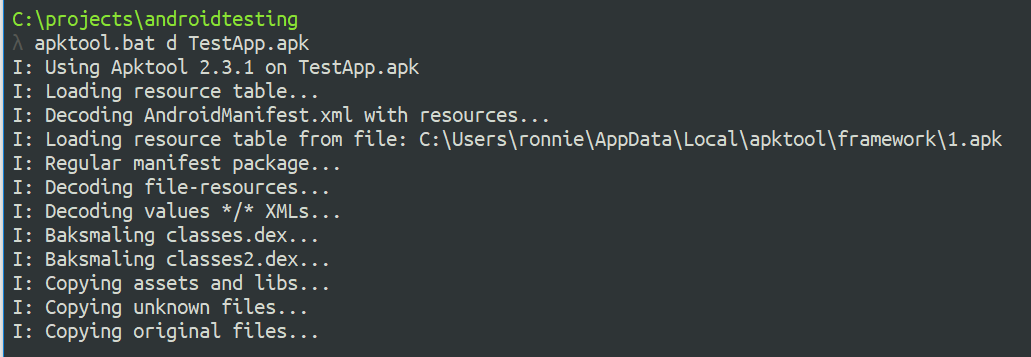
Next, add a new network security config by creating the file network_security_config.xml in the res/xml directory:
The config needs to explicitly state that trusting user certs is acceptable. The entire contents should be:
Finally, we have to define the network security config in AndroidManifest.xml . In the tag, add the android:networkSecurityConfig attribute pointing to the new XML file:
Reassemble and Sign Finally, the APK must now be rebuilt and signed in order to be installed. Using apktool b , a new build will be created in the dist/ directory:
To self-sign the app, use keytool to create a new keystore and key, then jarsigner to sign the new APK:
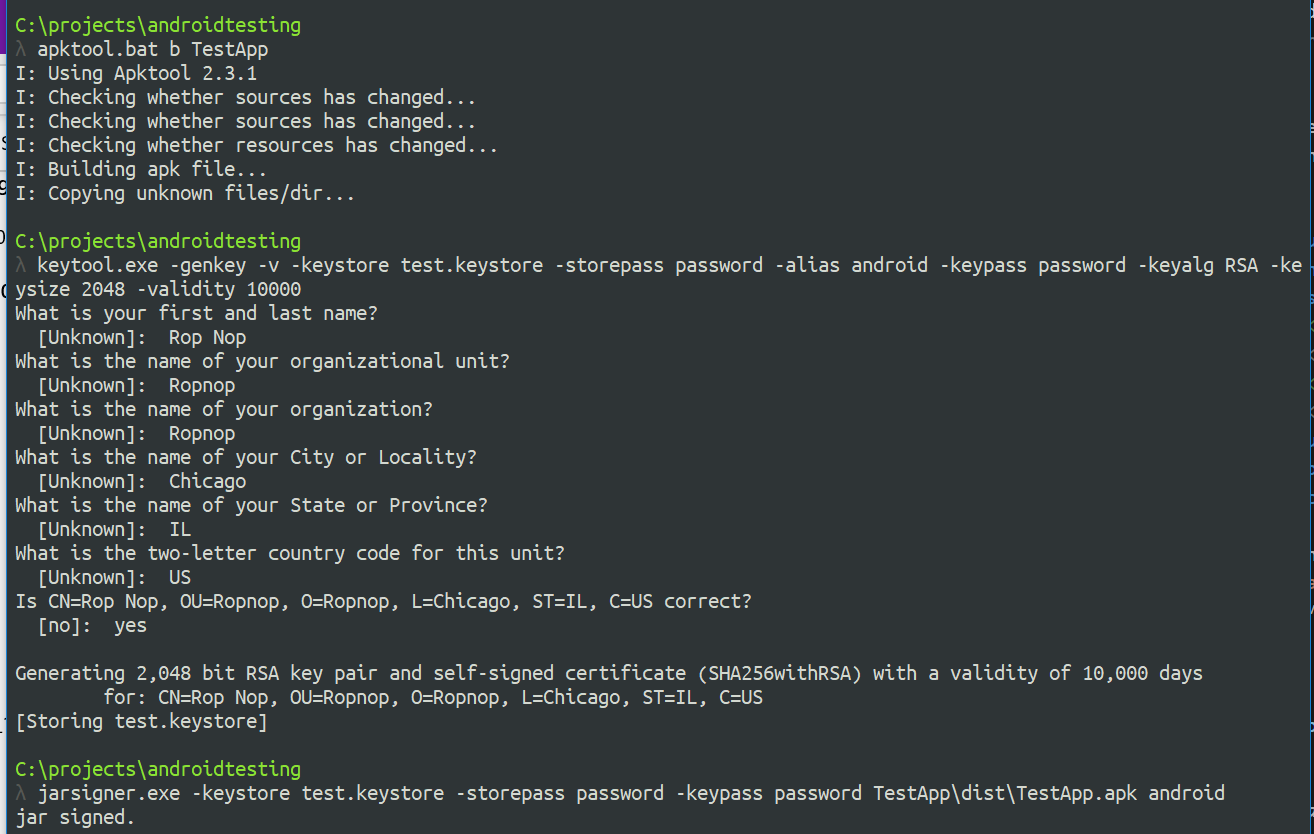
Lastly, install the new APK with adb :
Now, when we start the application, the logcat output will indicate a new network security config is being used:

With the Burp CA installed to user certificates, we can now MitM the application traffic!
Источник