- Книжная полка компьютерного криминалиста: 11 лучших книг по Digital Forensics, Incident Response и Malware Analysis
- 1. File Systems Forensic Analysis
- 2. Incident Response & Computer Forensics (третье издание)
- 3. Investigating Windows Systems
- 4. Digital Forensics and Incident Response (второе издание)
- 5. Windows Forensics Cookbook
- 6. The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and Mac Memory
- 7. Network Forensics
- 8. Practical Mobile Forensics: Forensically investigate and analyze iOS, Android, and Windows 10 devices (четвертое издание)
- 9. Learning Android Forensics: Analyze Android devices with the latest forensic tools and techniques (второе издание)
- 10. Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware
- 11. Rootkits and Bootkits: Reversing Modern Malware and Next Generation Threats
- Learning Android Forensics
- Book Description:
- Learning Android Forensics — Second Edition
- About this book
- Related Tags:
- Introducing Android Forensics
- Mobile forensics
- The mobile forensics approach
- Investigation preparation
- Seizure and isolation
- The acquisition phase
- Examination and analysis
- Reporting
- Challenges in mobile forensics
- Android architecture
- The Linux kernel
- Hardware abstraction level
- Android Runtime
- Native C/C++ Libraries
- Java API Framework
- The application layer
- Android security
- Security at OS level through the Linux kernel
Книжная полка компьютерного криминалиста: 11 лучших книг по Digital Forensics, Incident Response и Malware Analysis
Хотите разобраться в компьютерной или мобильной криминалистике? Научиться реагированию на инциденты? Реверсу вредоносных программ? Проактивному поиску угроз (Threat Hunting)? Киберразведке? Подготовиться к собеседованию? В этой статье Игорь Михайлов, специалист Лаборатории компьютерной криминалистики Group-IB, собрал топ-11 книг по компьютерной криминалистике, расследованию инцидентов и реверсу вредоносных программ, которые помогут изучить опыт профессионалов, прокачать свои скиллы, получить более высокую должность или новую высокооплачиваемую работу.
Когда я пришел в компьютерную экспертизу — а это был в 2000 год — из методической литературы у специалистов было только 71 страничное пособие: «Общие положения по назначению и производству компьютерно-технической экспертизы: Методические рекомендации», выпущенное МВД России и ряд публикаций в различных периодических изданиях. И даже эти немногие материалы были доступны лишь ограниченному кругу. Приходилось искать, ксерокопировать, переводить иностранные книги по форензике — литература достойного качества по этой теме на русском языке отсутствовала.
Сейчас ситуация немного другая. Литературы очень много, как и раньше она преимущественно на английском языке. И чтобы сориентироваться в этом море информации, чтобы в 101 раз не перечитывать книгу, содержащую материал начального уровня, я подготовил эту подборку, изучить которую будет полезно как начинающим, так и профессионалам.
1. File Systems Forensic Analysis
автор: Brian Carrier

В своей работе автор использовал такой известнейший криминалистический инструмент, как Sleuth Kit (TSK), разработанный им на основе The Coroner’s Toolkit. Любой желающий может повторить шаги, проделанные автором с помощью этого инструмента, или провести свои исследования. Графическая оболочка Sleuth Kit — программа Autopsy — широко применяется для криминалистического анализа цифровых доказательств и расследования инцидентов.
Эта книга переведена на русский язык под названием «Криминалистический анализ файловых систем». Но будьте аккуратны с изложенной в ней информацией, так как в переводе есть неточности, которые в некоторых случаях серьезно искажают смысл.
2. Incident Response & Computer Forensics (третье издание)
авторы: Jason T. Luttgens, Matthew Pepe, Kevin Mandia

Книга получилась настолько хорошей, что ее включили в комплект учебных материалов по курсу SANS «FOR508: Advanced Incident Response, Threat Hunting, and Digital Forensics» — топовому учебному курсу по расследованию инцидентов.
Существует переводное издание этой книги: «Защита от вторжений. Расследование компьютерных преступлений». Перевод издан в России двумя тиражами. Но поскольку переводилась первая версия книги, информация в ней устарела.
3. Investigating Windows Systems
автор: Harlan Carvey

4. Digital Forensics and Incident Response (второе издание)
автор: Gerard Johansen

Дополнительно читатель получит базовое представление об исследовании системных журналов, узнает принципы реверса вредоносных программ, основы проактивного поиска угроз (Threat Hunting’а) и киберразведки (Threat Intelligence), а также ознакомится с правилами написания отчетов.
5. Windows Forensics Cookbook
авторы: Oleg Skulkin, Scar de Courcier

6. The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and Mac Memory
автор: Michael Hale Ligh

Рекомендуется к прочтению тем, кто решил максимально подробно разобраться в том, какие криминалистические артефакты можно найти в оперативной памяти.
7. Network Forensics
автор: Ric Messier

8. Practical Mobile Forensics: Forensically investigate and analyze iOS, Android, and Windows 10 devices (четвертое издание)
авторы: Rohit Tamma, Oleg Skulkin, Heather Mahalik, Satish Bommisetty

9. Learning Android Forensics: Analyze Android devices with the latest forensic tools and techniques (второе издание)
авторы: Oleg Skulkin, Donnie Tindall, Rohit Tamma

10. Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware
автор: Monnappa K. A.

Читатель узнает, как настроить свою лабораторию для анализа вредоносных программ, ознакомится с методами статического и динамического анализа подобных программ, получит уроки работы с интерактивным дизассемблером IDA Pro, узнает, как обходить обфускацию — технологию, усложняющую изучение исходного кода программ.
Эта книга доступна в переводе на русском языке: «Анализ вредоносных программ».
11. Rootkits and Bootkits: Reversing Modern Malware and Next Generation Threats
авторы: Alex Matrosov, Eugene Rodionov, Sergey Bratus

Читатель ознакомится с такими темами, как процесс загрузки 32- и 64-разрядных операционных систем Windows, на примерах вместе с авторами разберет методы анализа конкретных руткитов и буткитов, узнает о векторах атак на BIOS и UEFI и разработке методов детектирования подобных атак, узнает о применении виртуализации для анализа поведения буткитов.
Источник
Learning Android Forensics
Book Description:
Many forensic examiners rely on commercial, push-button tools to retrieve and analyze data, even though there is no tool that does either of these jobs perfectly. This book will introduce you to the Android platform and its architecture, and provides a high-level overview of what Android forensics entails. You will see how data is stored on Android devices and how to set up a digital forensic examination environment. Next, you will go through the various physical and logical techniques to extract data from devices to obtain forensic evidence. You will also learn how to reverse-engineer applications and forensically analyze the data with the help of various open source and commercial tools.
By the end of this book, you will have a complete understanding of the Android forensic process.
What You Will Learn
- Understand the Android system architecture and its significance for Android forensics
- Build a forensically sound workstation
- Utilize ADB to acquire data
- Bypass Android security such as PINs and passwords
- Perform both logical and full physical extractions to retrieve data
- Reverse-engineer applications
- Analyze data from many popular applications including Gmail, WhatsApp, and Snapchat
- Discover free and open source tools to aid in data acquisition and analysis
You can also get this PDF by using our Android Mobile App directly: 
Источник
Learning Android Forensics — Second Edition
Introducing Android Forensics
Setting up the Android Forensic Environment
Understanding Data Storage on Android Devices
Extracting Data Logically from Android Devices
Extracting Data Physically from Android Devices
Recovering Deleted Data from an Android Device
Forensic Analysis of Android Applications
Android Forensic Tools Overview
Identifying Android Malware
Android Malware Analysis
Other Books You May Enjoy
About this book
Many forensic examiners rely on commercial, push-button tools to retrieve and analyze data, even though there is no tool that does either of these jobs perfectly.
Learning Android Forensics will introduce you to the most up-to-date Android platform and its architecture, and provide a high-level overview of what Android forensics entails. You will understand how data is stored on Android devices and how to set up a digital forensic examination environment. As you make your way through the chapters, you will work through various physical and logical techniques to extract data from devices in order to obtain forensic evidence. You will also learn how to recover deleted data and forensically analyze application data with the help of various open source and commercial tools. In the concluding chapters, you will explore malware analysis so that you’ll be able to investigate cybersecurity incidents involving Android malware.
By the end of this book, you will have a complete understanding of the Android forensic process, you will have explored open source and commercial forensic tools, and will have basic skills of Android malware identification and analysis.
Related Tags:
Introducing Android Forensics
Mobile forensics is a branch of digital forensics that is evolving in today’s digital era and is constantly changing as new phones are released and operating systems are updated. Android forensics deals with extracting, recovering, and analyzing data present on an Android device through various techniques. Due to the open nature of the Android operating system, these forensic techniques and methods can apply to more than just mobile phones: refrigerators, vehicle entertainment units, televisions, watches, and many more devices run Android.
It’s important to have a clear understanding of the platform and other fundamentals before we dive in and find out how to extract data. In this chapter, we’ll cover the following:
- Mobile forensics
- The mobile forensics approach
- Challenges in mobile forensics
- Android architecture
- Android security
- Android hardware components
- Android boot process
The world today is experiencing technological innovation like never before, and this growth is almost exponential in the field of mobile devices. Gartner, a technology research and advisory firm, in their forecasts published in January 2018, estimated that mobile phone shipments in 2017 totaled 2.28 billion units and would increase to 2.32 billion in 2018. This statistic alone reflects the unprecedented growth of mobile devices. Mobile phones have not only increased in number but also have become more sophisticated in terms of functionality. The increase of mobile phone subscribers from 1997 to 2018 is significantly high.
You probably don’t need to be told that smartphones are an increasingly large subset of mobile phones. The improvements in the computing power and data storage of these devices enable us to perform a wide range of activities, and we are increasingly becoming dependent on these mobile devices. Apart from performing routine tasks such as making calls and sending messages, and so on, these devices also support other activities such as sending emails, surfing the internet, recording videos, creating and storing documents, identifying locations with Global Positioning System (GPS) services, and managing business tasks. In other words, mobile devices are now repositories of sensitive personal information.
Quite often, the data sitting in a device is more valuable than the device itself. Imagine a case involving the smartphone of a suspected terrorist; how useful would it be for law enforcement to access every contact, call, SMS, or email that the suspect had sent or received? Or, perhaps even better, every location that the phone had been? While much of this data is generally available through the service provider, that often requires additional warrants or subpoenas and can take a significant amount of time. And consider third-party applications; WhatsApp chat content, for example, is end-to-end encrypted, and no amount of subpoenas to Facebook can recover that data. This book will show you how to recover data, such as WhatsApp chats, that may not be recoverable through any other method. The fact that mobile forensics played a crucial role in solving cases such as the 2010 Times Square car bombing attempt and Boston marathon bombings, reaffirms the increasing role of mobile forensics in solving many cases.
Mobile forensics
Mobile device forensics is a branch of digital forensics that deals with extracting, recovering, and analyzing digital evidence or data from a mobile device under forensically sound conditions. Simply put, it deals with accessing the data stored on devices, which includes SMS, contacts, call records, photos, videos, documents, application files, browsing history, and so on, and recovering data deleted from devices using various forensic techniques. It is important that the process of recovering or accessing details from a device is forensically sound if it has to be admitted in a court of law and to maintain the integrity of the evidence. If the evidence has to be admitted in a court of law, it’s important to work only on the image file and not on the original device itself.
The term forensically sound is often used in the digital forensics community to clarify the correct use of a particular forensic technology or methodology. Mobile forensics, especially Android forensics, is evolving fast, owing to the fact that it has a total the market share of 85 percent (as per market research firm, IDC).
As explained by Eoghan Casey, in his book Digital Forensics and Investigation, forensic soundness is not just about keeping the original evidence unaltered. Even the routine task of acquiring data from a hard drive using a hardware write blocker may cause alterations (for example, making a hidden area of the hard drive accessible) on the drive. One of the keys to forensic soundness is documentation. Documenting how the device is handled from the beginning is very important. Hence, an investigation can be considered forensically sound if the acquisition process preserves the original data and its authenticity and integrity can be validated. Evidence integrity checks ensure that the evidence has not been tampered with from the time it was collected. Integrity checks are done by comparing the digital fingerprint of the evidence taken at the time of collection with the digital fingerprint of the evidence in its current state.
There is a growing need for mobile forensics due to several reasons, some of which include the following:
- Use of mobile phones to store personal information
- Increased use of mobile phones to perform online activities
- Use of mobile phones in several crimes
Mobile forensics on a particular device is primarily dependent on the underlying operating system. Hence, we have different fields such as Android forensics, iOS forensics, and so on.
The mobile forensics approach
Once the data is extracted from a device, different methods of analysis are used based on the underlying case. As each investigation is distinct, it is not possible to have a single definitive procedure for all of the cases. However, the overall process can be broken down into five phases, as shown in the following diagram:
The following section discusses each phase in detail.
Investigation preparation
This phase begins when a request for examination is received. It involves preparing all of the paperwork and forms required to document chain of custody, ownership information, device model, purpose, information that the requestor is seeking, and so on. Chain of custody refers to the chronological documentation or paper trail, showing the seizure, custody, control, transfer, analysis, and disposition of physical or electronic evidence. From the details submitted by the requestor, it’s important to have a clear understanding of the objective for each examination.
Seizure and isolation
Handling the device during seizure is one of the important steps while performing forensic analysis. The evidence is usually transported using anti-static bags, which are designed to protect electronic components against damage produced by static electricity. As soon as the device is seized, care should be taken to make sure that our actions don’t result in any data modification on the device. At the same time, any opportunity that can aid the investigation should also not be missed. The following are some of the points that need to be considered while handling an Android device during this phase:
- With increasing user awareness of security and privacy, most devices now have screen lock enabled. During the time of seizure, if there is a chance (for instance, the phone is recovered unlocked), disable the passcode. Some of the devices don’t ask the user to reenter the passcode while disabling the lock screen option.
- If the device is unlocked, try to change the settings of the device to allow greater access to the device. The following are some of the settings that can be considered to achieve this:
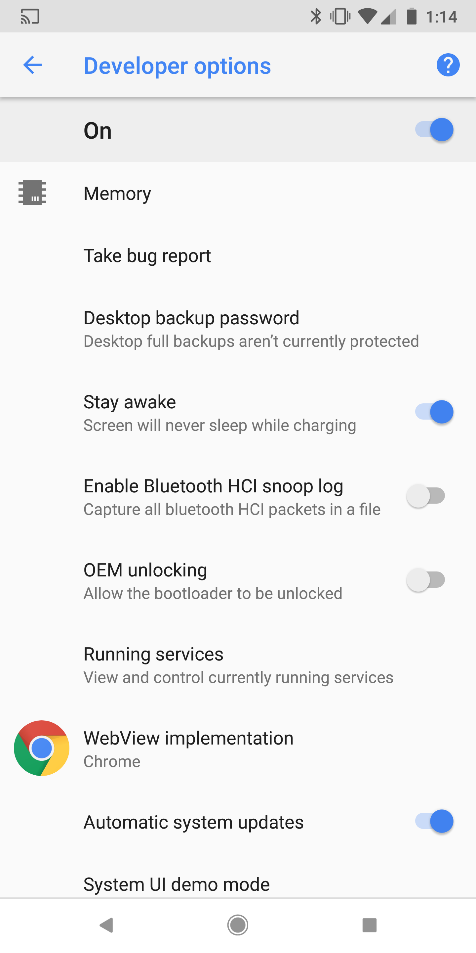
- Enable USB debugging: Enabling this option gives greater access to the device through the Android Debug Bridge (ADB) connection. We are going to cover the ADB in detail in Chapter 2, Setting Up the Android Forensic Environment. This will greatly aid the forensic investigator during the data extraction process. In Android devices, this option is usually found under Settings | Developer options , as shown in the following screenshot. On newer Android versions starting from 4.2, developer options are hidden by default. To enable them, navigate to Settings | About Phone (or Settings | System | About Phone on Android 8.0 or higher )and tap on the Build number seven times.
- Enable the Stay Awake setting: Enabling this option and charging the device will make the device stay awake; in other words, it doesn’t get locked. In Android devices, this option is usually found under Settings | Developer options , as shown in the following screenshot:
-
- Increase screen timeout: This is the time for which the device will be active once it is unlocked. Depending on the device model, this time can be set up to 30 minutes. In most devices, it can be accessed under Settings | Display | Screen Timeout.
Please note that the location to access these items changes across different versions and models of Android phones and may not be available in all versions.
In mobile forensics, it is of crucial importance to protect the seized device so that our interaction with the evidence (or, for that matter, an attacker’s attempt to remotely interact with the device) doesn’t change the evidence. In computer forensics, we have software and hardware write blockers that can perform this function. But in mobile forensics, since we need to interact with the device to pull the data, these write blockers are not of any use. Another important aspect is that we also need to prevent the device from interacting with a wireless radio network. As mentioned earlier, there is a high probability that an attacker can issue remote wipe commands to delete all of the data including emails, applications, photos, contacts, and other files on the device.
The Android Device Manager and several other third party apps allow the phone to be remotely wiped or locked. This can be done by signing into the Google account that is configured on the mobile. Using this software, an attacker can also locate the device that could pose a security risk. For all of these reasons, isolating the device from all communication sources is very important.
Have you thought about remote wipe options without using the internet? Mobile Device Management (MDM) software, commonly used by companies to manage corporate devices, can provide remote wipe features just by sending an SMS. Isolating the device from all communication options is crucial.
To isolate the device from a network, we can put the device in Airplane mode if we have access to the device. Airplane mode disables a device’s wireless transmission functions such as cellular radio, Wi-Fi, and Bluetooth. However, as Wi-Fi is now available in airplanes, some devices now allow Wi-Fi access in Airplane mode. The following screenshot shows the quick settings available by dragging down the top menu bar from the lock screen:
An alternate solution would be to use a Faraday bag or RF isolation box, as both effectively block signals to and from the mobile phone. One concern with these isolation methods is that, once they’re employed, it is difficult to work with the phone because you cannot see through it to use the touchscreen or keypad. For this reason, Faraday tents and rooms exist, as shown in the following screenshot:
Even after taking all of these precautions, certain automatic functions such as alarms can still trigger. If such a situation is encountered, it must be properly documented.
The acquisition phase
The acquisition phase refers to extraction of data from the device. Due to the inherent security features of mobile devices, extracting the data is not always straightforward. The extraction method is decided largely depending on the operating system, make, and model. The following are the types of acquisition methods that can be used to extract data from a device:
- Manual acquisition is the simplest of all of the acquisition methods. The examiner uses the user interface of the phone to browse and investigate. No special tools or techniques are required here, but the limitation is that only the files and data visible through the normal user interface can be extracted. Data extracted through other methods can also be verified using this. It should be noted that this option can very easily modify data on the device (for instance, opening an unread SMS will mark it as read), so these changes should be documented as thoroughly as possible.
- Logical acquisition, also called logical extraction, generally refers to extracting the files that are present on a logical store such as a file system partition. This involves obtaining data types such as text messages, call history, and pictures from a phone. The logical extraction technique works by using the original equipment manufacturer Applications Programming Interfaces (APIs) for synchronizing the phone’s contents with a computer. This technique usually involves extracting the following evidence:
- Call logs
- SMS
- MMS
- Browser history
- People
- Contact methods
- Contacts extensions
- Contacts groups
- Contacts phones
- Contacts setting
- External Image Media (metadata)
- External Image Thumbnail Media (metadata)
- External Media, Audio, and Misc. (metadata)
- External Videos (meta data)
- MMSParts (includes full images sent via MMS)
- Location details (GPS data)
- Internet activity
- Organizations
- List of all applications installed and their versions
- Social networking app data such as WhatsApp, Skype, and Facebook
- File System acquisition is a logical procedure and generally refers to the extraction of a full file system from a mobile device. File system acquisition can sometimes help in recovering the contents (stored in SQLite files) that are deleted from the device.
- Physical acquisition involves making a bit-for-bit copy of an entire flash storage device, equivalent to a full image of a hard drive. The data extracted using this method is usually in the form of raw data (as a hexadecimal dump) that can then be further parsed to obtain file system information or human-readable data. Since all investigations are performed on this image, this process also ensures that an original evidence is not altered.
Examination and analysis
In this phase, different software tools are used to extract the data from the memory image. In addition to the tools, an investigator may also need the help of a hex editor, as tools do not always extract all of the data. There is no single tool that can be used in all cases. Hence, examination and analysis requires a sound knowledge of various file systems, file headers, and so on.
Reporting
Documentation of the examination should be done throughout the process, noting down what was done in each phase. The following are a few points that might be documented by an examiner:
- The date and time the examination started
- The physical condition of the phone
- The status of the phone when received (ON/OFF)
- The make, model, and operating system of the phone
- Pictures of the phone and individual components
- The tools used during the investigation (including the version number)
- Data documented during the examination
The data extracted from the mobile device should be clearly presented to the recipient so that it can be imported into other software for further analysis. In the case of civil or criminal cases, wherever possible, pictures of data as it existed on the cellular phone should be collected, as they are visually compelling to a jury.
Challenges in mobile forensics
With the increased usage of Android devices and the wider array of communication platforms they support, the demand for forensic examination automatically has grown. While working with mobile devices, forensic analysts face a number of challenges. The following points shed light on some of the mobile forensics challenges faced today:
- Preventing data alteration on the device: One of the fundamental rules to remember in forensics is to preserve the original evidence. In other words, the forensic techniques that are applied on a device to extract any information should not alter the data present on the device. However, this is usually not practical with respect to mobile forensics because simply switching on a device might also change certain state variables present on the device. With mobile devices, background processes always run, and a sudden transition from one state to another can result in the loss or modification of data. Hence, there’s a chance that data may be altered either intentionally or unintentionally by the forensic analyst. Apart from this, there is a high possibility that an attacker (or the user) can remotely change or delete the contents of the device. As mobile phones use different communication channels (cellular, Wi-Fi, Bluetooth, infrared, and so on), the possibility of communicating through them should be eliminated. Features such as remote data wiping would enable an attacker to remotely wipe the entire device just by sending an SMS or by simply pressing a button that sends a wipe request to the Android device. Unlike computer forensics, mobile device forensics requires more than just isolating the device from the network, and phones cannot always be left powered off during examination.
- The wide range of operating systems and device models: The wide range of mobile operating systems available in the market makes the life of a forensic analyst more difficult. Although Android is the most dominant operating system in the mobile world, there are mobile devices that run on other operating systems including iOS, Blackberry, and Windows, that are often encountered during investigations. Also, for a given operating system, there are millions of mobile devices available that differ in OS versions, hardware, and various other features. Based on manufacturer, the approach to acquire forensic artifacts changes. To remain competitive, manufacturers release new models and updates so rapidly that it’s hard to keep a track of all of them. Sometimes, within the same operating system the data storage options and file structures also change, making it even more difficult. There’s no single tool that can work on all the available types of mobile operating systems. Hence, it is crucial for forensic analysts to remain updated on all of the latest changes and techniques, and to understand the underlying concepts in this book so they can succeed when the tools fail.
Inherent security features: As the concept of privacy is increasingly gaining importance, mobile manufacturers are moving towards implementing robust security controls on devices, which complicates the process of gaining access to the data. For example, if the device is passcode protected, the forensic investigator has to first find a way to bypass the passcode. Similarly, full disk encryption mechanisms implemented on many modern devices prevent law enforcement agencies and forensic analysts from accessing the information on the device. Apple’s iPhone encrypts all of the data present on the device by default using hardware keys built into the device. Beginning with Android Nougat, Android forces full disk encryption by default (though it can vary if the OS is modified by the manufacturer). At Google’s 2017 I/O conference, they announced that 80% of Android 7.0 Nougat devices were encrypted and 70% used a secure lock screen. These numbers will likely continue to grow as encryption is forced by more manufacturers during the initial setup process. It is very difficult for an examiner to break these encryption mechanisms using techniques such as brute force.
Legal issues: Mobile devices can be involved in crimes that span across the globe and can cross geographical boundaries. In order to tackle these multi-jurisdictional issues, the forensic examiner needs to be aware of the nature of the crime and regional laws.
Android architecture
Before we proceed with the internals of Android forensics, this section will introduce you to Android as an operating system and will cover various fundamental concepts that need to be understood to gain experience in the area of forensics.
Any operating system (desktop or mobile phone) assumes the responsibility for managing the resources of the system and provides a way for applications to talk to hardware or physical components in order to accomplish certain tasks. The Android operating system is no different. It powers mobile phones, manages memory and processes, enforces security, takes care of networking issues, and so on. Android is open source and most of the code is released under the Apache 2.0 license. Practically, this means mobile phone device manufacturers can access it, freely modify it, and use the software according to the requirements of any device. This is one of the primary reasons for its spread in popularity.
The Android operating system consists of a stack of layers running one above the other. Android architecture can be best understood by taking a look at what these layers are and what they do. The following screenshot (courtesy of http://developer.android.com), shows the various layers involved in the Android software stack:
Android architecture is in the form of a software stack comprising kernels, libraries, runtime environment, applications, middleware, and services. Each layer of the stack and elements within each layer, are integrated in a way to provide the optimal execution environment for mobile devices. The following sections focus on different layers of the Android stack, starting at the bottom with the Linux kernel.
The Linux kernel
The Android OS is built on top of the Linux kernel with some architectural changes made by Google. Linux was chosen as it is a portable platform that can be compiled easily on different hardware. The Linux kernel is positioned at the bottom of the software stack and provides a level of abstraction between the device hardware and the upper layers. It also acts as an abstraction layer between the software and hardware present on the device. To understand this better, consider the case of a camera click. What actually happens when you take a photo using the camera button on your mobile device? At some point, the hardware instruction (pressing a button) has to be converted into a software instruction (to take a picture and store it in the gallery). The kernel contains drivers that can facilitate this process. When the camera button click is detected, the instruction goes to the corresponding driver in the kernel, which sends the necessary commands to the camera hardware, similar to what occurs when a key is pressed on a keyboard. In simple terms, the drivers in the kernel control the underlying hardware. As shown in the previous screenshot, the kernel contains drivers related to Wi-Fi, Bluetooth, USB, audio, display, and so on.
All of the core functionalities of Android, such as process management, memory management, security, and networking are managed by the Linux kernel. Linux is a proven platform when it comes to both security and process management. Android has leveraged the existing Linux open source OS to build a solid foundation for its ecosystem. Each version of Android has a different version of the underlying Linux kernel. Currently, Google requires devices shipped with the Android 8.0 Oreo OS to have at least Linux kernel version 4.4.
Hardware abstraction level
The hardware abstraction level or HAL allows the higher level, Java API framework, to work with mobile device’s hardware with help of standard interfaces. This can be done thanks to multiple library modules, which provide interfaces for different types of hardware components, like Bluetooth or camera.
Android Runtime
Since Android 5.0 each application runs in its own process and with its own instance of the Android Runtime (ART) . It allows run multiple virtual machines on low-memory devices by executing DEX (Dalvik Executable) files. It’s important to note that prior to version 5.0 Dalvik was Android Runtime, so applications developed for Dalvik should work when running with ART.
Native C/C++ Libraries
Many core Android system components and services, including those mentioned earlier, like HAL and ART, are built from native code, so they require native libraries written in C and C++.
Java API Framework
Java API framework allows developers to create applications using modular system components and services as building blocks:
- View System allows to build application’s user interface, and includes lists, grids, text boxes, buttons, and so on.
- Resource Manager provides access to non-code components of an application, like localized strings, graphics and layout files.
- Notification Manager allows applications to display custom alerts.
- Activity Manager manages the lifecycle as applications, and their back stack — the order in which each activity is opened.
- Content Providers allows applications to access other applications data, and share their own.
The application layer
The topmost layer in the Android stack consists of applications (called apps), which are programs that users directly interact with. There are two kinds of apps, as discussed here:
- System apps: These are applications that are pre-installed on the phone and are shipped along with the phone. Applications such as default browser, email client, and contacts are examples of system apps. These generally cannot be uninstalled or changed by the user as they are read-only on production devices, though some devices offer the ability to disable these applications. If a system application is disabled, the app and all of its data remain on the device on the system partition, the application icon is simply hidden from the user. These applications can usually be found in the /system partition. Until Android 4.4 Kit Kat, all apps present under /system were treated equally. Beginning in Android 4.4, apps installed in /system/priv-app/ are treated as privileged applications and are granted permissions with protection-level signatureOrSystem to privileged apps.
- User installed apps: These are the applications that are downloaded and installed by the user from various distribution platforms such as Google Play. Google Play is the official app store for the Android operating system, where users can browse and download the applications. Based on December 2017 statistics from Statista, there are around 3.5 million Android apps in the Play Store. These apps are present under the /data partition. More information about how security is enforced between them is discussed in the following sections.
Android security
Android as a platform has certain features built into the architecture that ensure the security of users, applications, and data. Although they help in protecting the data, these security features sometimes prevent investigators from getting access to necessary data. From a forensic perspective, it is first important to understand the inherent security features so that a clear idea is established about what can be or cannot be accessed under normal circumstances. The security features and offerings that are incorporated aim to achieve three things:
- To protect user data
- To protect system resources
- To make sure that one application cannot access the data of another application
The next sections provide an overview of the key security features in the Android operating system.
Security at OS level through the Linux kernel
The Android operating system is built on top of the Linux kernel. Over the past few decades, Linux has evolved as a secure operating system trusted by many corporations across the world for its security. By having the Linux kernel at the heart of its platform, Android tries to ensure security at the OS level. Also, Android has built a lot of specific code into Linux to include certain features related to the mobile environment. With each Android release the kernel version also has changed. The following table shows Android versions and the corresponding Linux kernel version:
Источник