- Signing Your Applications
- In this document
- See also
- Signing Overview
- Signing in Debug Mode
- Signing in Release Mode
- Signing Android Wear Apps
- Signing Your App in Android Studio
- Automatically Signing Your App
- Signing Considerations
- Securing Your Private Key
- Expiry of the Debug Certificate
- Signing Your App Manually
- Add self signed SSL certificate to Android (for browsing)
- Installing self-signed certificates on Android
- Generate a self-signed TLS CA Certificate
- Formatting the certificate
- Installing the certificate on the Android device
- Sign up for more like this.
- Why embedding secrets in mobile apps is not a good idea
- About Canada’s COVID Alert application
- OPSEC tips for the general public
Signing Your Applications
In this document
See also
Android requires that all apps be digitally signed with a certificate before they can be installed. Android uses this certificate to identify the author of an app, and the certificate does not need to be signed by a certificate authority. Android apps often use self-signed certificates. The app developer holds the certificate’s private key.
Signing Overview
You can sign an app in debug or release mode. You sign your app in debug mode during development and in release mode when you are ready to distribute your app. The Android SDK generates a certificate to sign apps in debug mode. To sign apps in release mode, you need to generate your own certificate.
Signing in Debug Mode
In debug mode, you sign your app with a debug certificate generated by the Android SDK tools. This certificate has a private key with a known password, so you can run and debug your app without typing the password every time you make a change to your project.
Android Studio signs your app in debug mode automatically when you run or debug your project from the IDE.
You can run and debug an app signed in debug mode on the emulator and on devices connected to your development manchine through USB, but you cannot distribute an app signed in debug mode.
By default, the debug configuration uses a debug keystore, with a known password and a default key with a known password. The debug keystore is located in $HOME/.android/debug.keystore, and is created if not present. The debug build type is set to use this debug SigningConfig automatically.
For more information about how to build and run apps in debug mode, see Building and Running.
Signing in Release Mode
In release mode, you sign your app with your own certificate:
- Create a keystore. A keystore is a binary file that contains a set of private keys. You must keep your keystore in a safe and secure place.
- Create a private key. A private key represents the entity to be identified with the app, such as a person or a company.
Add the signing configuration to the build file for the app module:
The package in app/build/apk/app-release.apk is now signed with your release key.
Note: Including the passwords for your release key and keystore inside the build file is not a good security practice. Alternatively, you can configure the build file to obtain these passwords from environment variables or have the build process prompt you for these passwords.
To obtain these passwords from environment variables:
To have the build process prompt you for these passwords if you are invoking the build from the command line:
After you complete this process, you can distribute your app and publish it on Google Play.
Warning: Keep your keystore and private key in a safe and secure place, and ensure that you have secure backups of them. If you publish an app to Google Play and then lose the key with which you signed your app, you will not be able to publish any updates to your app, since you must always sign all versions of your app with the same key.
The rest of this document provides detailed instructions about how to generate a private key and sign your apps in release mode with Android Studio.
Signing Android Wear Apps
When publishing Android Wear apps, you package the wearable app inside of a handheld app, because users cannot browse and install apps directly on the wearable. Both apps must be signed. For more information on packaging and signing Android Wear apps, see Packaging Wearable Apps.
Signing Your App in Android Studio
To sign your app in release mode in Android Studio, follow these steps:
- On the menu bar, click Build >Generate Signed APK.
On the Generate Signed APK Wizard window, click Create new to create a new keystore.
If you already have a keystore, go to step 4.
On the New Key Store window, provide the required information as shown in figure 1.
Your key should be valid for at least 25 years, so you can sign app updates with the same key through the lifespan of your app.
Figure 1. Create a new keystore in Android Studio.
On the Generate Signed APK Wizard window, select a keystore, a private key, and enter the passwords for both. Then click Next.
Figure 2. Select a private key in Android Studio.
On the next window, select a destination for the signed APK and click Finish.
Figure 3. Generate a signed APK in Android Studio.
Automatically Signing Your App
In Android Studio, you can configure your project to sign your release APK automatically during the build process:
- On the project browser, right click on your app and select Open Module Settings.
- On the Project Structure window, select your app’s module under Modules.
- Click on the Signing tab.
Select your keystore file, enter a name for this signing configuration (as you may create more than one), and enter the required information.
Figure 4. Create a signing configuration in Android Studio.
Under Signing Config, select the signing configuration you just created.
Figure 5. Select a signing configuration in Android Studio.
You can also specify your signing settings in Gradle configuration files. For more information, see Configuring Gradle Builds.
Signing Considerations
You should sign all of your apps with the same certificate throughout the expected lifespan of your applications. There are several reasons why you should do so:
- App upgrade: When the system is installing an update to an app, it compares the certificate(s) in the new version with those in the existing version. The system allows the update if the certificates match. If you sign the new version with a different certificate, you must assign a different package name to the application—in this case, the user installs the new version as a completely new application.
- App modularity: Android allows apps signed by the same certificate to run in the same process, if the applications so requests, so that the system treats them as a single application. In this way you can deploy your app in modules, and users can update each of the modules independently.
- Code/data sharing through permissions: Android provides signature-based permissions enforcement, so that an app can expose functionality to another app that is signed with a specified certificate. By signing multiple apps with the same certificate and using signature-based permissions checks, your apps can share code and data in a secure manner.
If you plan to support upgrades for an app, ensure that your key has a validity period that exceeds the expected lifespan of that app. A validity period of 25 years or more is recommended. When your key’s validity period expires, users will no longer be able to seamlessly upgrade to new versions of your application.
If you plan to publish your apps on Google Play, the key you use to sign these apps must have a validity period ending after 22 October 2033. Google Play enforces this requirement to ensure that users can seamlessly upgrade apps when new versions are available.
Securing Your Private Key
Maintaining the security of your private key is of critical importance, both to you and to the user. If you allow someone to use your key, or if you leave your keystore and passwords in an unsecured location such that a third-party could find and use them, your authoring identity and the trust of the user are compromised.
If a third party should manage to take your key without your knowledge or permission, that person could sign and distribute apps that maliciously replace your authentic apps or corrupt them. Such a person could also sign and distribute apps under your identity that attack other apps or the system itself, or corrupt or steal user data.
Your private key is required for signing all future versions of your app. If you lose or misplace your key, you will not be able to publish updates to your existing appn. You cannot regenerate a previously generated key.
Your reputation as a developer entity depends on your securing your private key properly, at all times, until the key is expired. Here are some tips for keeping your key secure:
- Select strong passwords for the keystore and key.
- Do not give or lend anyone your private key, and do not let unauthorized persons know your keystore and key passwords.
- Keep the keystore file containing your private key in a safe, secure place.
In general, if you follow common-sense precautions when generating, using, and storing your key, it will remain secure.
Expiry of the Debug Certificate
The self-signed certificate used to sign your application in debug mode has an expiration date of 365 days from its creation date. When the certificate expires, you will get a build error.
To fix this problem, simply delete the debug.keystore file. The default storage location is in
/.android/ on OS X and Linux, in C:\Documents and Settings\ \.android\ on Windows XP, and in C:\Users\ \.android\ on Windows Vista and Windows 7.
The next time you build, the build tools will regenerate a new keystore and debug key.
Note that, if your development machine is using a non-Gregorian locale, the build tools may erroneously generate an already-expired debug certificate, so that you get an error when trying to compile your application. For workaround information, see the troubleshooting topic I can’t compile my app because the build tools generated an expired debug certificate.
Signing Your App Manually
You do not need Android Studio to sign your app. You can sign your app from the command line using standard tools from the Android SDK and the JDK. To sign an app in release mode from the command line:
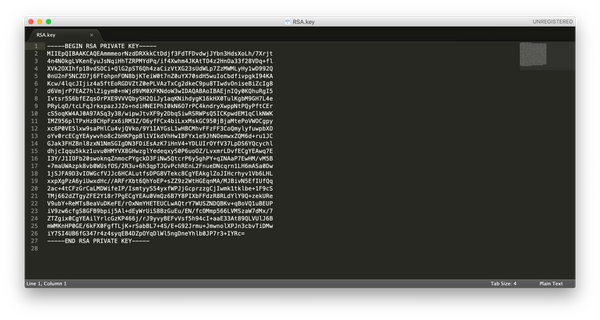
Generate a private key using keytool . For example:
This example prompts you for passwords for the keystore and key, and to provide the Distinguished Name fields for your key. It then generates the keystore as a file called my-release-key.keystore . The keystore contains a single key, valid for 10000 days. The alias is a name that you will use later when signing your app.
Compile your app in release mode to obtain an unsigned APK.
Sign your app with your private key using jarsigner :
This example prompts you for passwords for the keystore and key. It then modifies the APK in-place to sign it. Note that you can sign an APK multiple times with different keys.
Verify that your APK is signed. For example:
Align the final APK package using zipalign .
zipalign ensures that all uncompressed data starts with a particular byte alignment relative to the start of the file, which reduces the amount of RAM consumed by an app.
Источник
Add self signed SSL certificate to Android (for browsing)
Some people are developers. Some of them have secure sites. What’s more incredible, some want to test their websites on mobile phones with a environment as similar as possible to the production one, so they want to use a self-signed SSL certificate. Then, why it’s so difficult to do it?
After much trial and error, here’s a bulletproof guide to do in on Linux:
- Open Firefox (I suppose it’s also possible with Chrome, but it’s easier for me with FF)
- Visit your development site with a self-signed SSL certificate.
- Click on the certificate (next to the site name)
- Click on «More information»
- Click on «View certificate»
- Click on «Details»
- Click on «Export. «
- Choose «X.509 Certificate whith chain (PEM)», select the folder and name to save it and click «Save»
- Go to command line, to the directory where you downloaded the pem file and execute «openssl x509 -inform PEM -outform DM -in .pem -out .crt«
- Copy the .crt file to the root of the /sdcard folder inside your Android device
- Inside your Android device, Settings > Security > Install from storage. It should detect the certificate and let you add it to the device
- Browse to your development site. The first time it should ask you to confirm the security exception. That’s all. The certificate should work with any browser installed on your Android (Browser, Chrome, Opera, Dolphin. )
Remember that if you’re serving your static files from a different domain (we all are page speed bitches) you also need to add the certificate for that domain.
Источник
Installing self-signed certificates on Android
One of the best trends these days is the shift to encrypted Internet traffic, aka Transport Layer Security or TLS, and mobile apps are not the exception, often when testing a mobile app we need/want to see the data being sent from and received on our mobile devices but since most of the apps are using TLS on their network requests we cannot just proxy the traffic and understand the communication between the app and its server.
Here is where the Man-in-the-Middle aka MitM approach comes handy. In order to see the traffic in plaintext we’ll need our proxy to seat in the middle of the communication between the server and the app and to serve a valid TLS Certificate to the app.
I’ll explain how to generate your own self-signed* TLS CA Certificate and install it on you Android device:
Generate a self-signed TLS CA Certificate
- We’ll use openssl to generate the key, in this case I’m using a key size of 3072 bits. Generate the key with the following command:
- Again, using openssl we’ll generate the certificate, in this case I’m using a sha256 Hash and 3650 days (10 years) for its validity. Generate the certificate with the following command:
- For make it easier to import in your proxy (let’s say Burp) we’ll bundle the private key and the certificate:
Formatting the certificate
- Get the hash of the certificate (something similar to ba4acff9 ) with the following command:
- Make a copy of the burp.pem :
- Rename it to the hash value with extension .0 . It should be somethig like this ba4acff9.0
Installing the certificate on the Android device
- Connect to your device and remount /system as read/write (by default Android mounts /system as read-only):
- Push the certificate to /system/etc/security/cacerts/ (you’ll need root privileges):
if you get an error either on adb root or adb push do the following:
- Push the cert to the tmp folder (no root privileges needed for that):
- Connect to your device and move the certo to /system/etc/security/cacerts/ :
- Change the cert permissions and ownership:
That’s it! now your certificate is part of the trusted Root CA certificates. Note: You might need to go to Settigns -> Security -> Encryption and enable the certificate.
*self-signed means you’ll generate the signing keys.
Photo by Adrien on Unsplash
Sign up for more like this.
Why embedding secrets in mobile apps is not a good idea
This is a somewhat complicated topic to cover, but I’ll try to go into detail on why, generally, this is not a good idea and you should avoid embedding secrets in your mobile applications as much as possible. tl;dr Anyone motivated enough will get these secrets and impersonate your
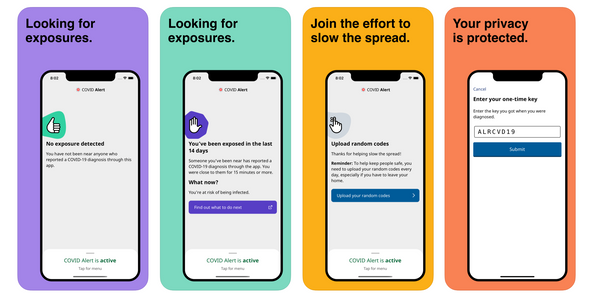
About Canada’s COVID Alert application
Disclaimer: First of all, I’m not writing on behalf of any entities involved in the development of the COVID Alert application. This is my take as a software engineer with some experience in mobile development. This post is aimed to people with some questions about this application but might not
OPSEC tips for the general public
It’s always a good idea to properly configure your computer and smartphone, know how to securely communicate with others and how to read, write and share content while protecting your personal information. These practices are more relevant than ever. OPSEC stands for operations security, taken from wikipedia: «Operations security
Источник