- Data encryption on Android with Jetpack Security
- Key Generation
- Unlocking time-bound keys
- Encrypt Files
- Encrypt SharedPreferences
- More Resources
- How to encrypt your Android device
- What is device encryption and what does it do?
- How to encrypt my Android device?
- Android 5.0 or higher
- Android 4.4 or lower
- And you’re done
- Extra options with third-party apps
- SSE – Universal Encryption App
- Crypto Ghost – File Encryption
- Safe Camera – Photo Encryption
- New Android security and encryption features
Data encryption on Android with Jetpack Security
Update: April 21st, 2021: Jetpack Security is now stable 1.0.0!
Update: December 2nd, 2021: Jetpack Security 1.1.0–Alpha-03 released, adding support for API level 21+ which includes a redesigned MasterKey implementation.
Have you ever tried to encrypt data in your app? As a developer, you want to keep data safe, and in the hands of the party intended to use. But if you’re like most Android developers, you don’t have a dedicated security team to help encrypt your app’s data properly. By searching the web to learn how to encrypt data, you might get answers that are several years out of date and provide incorrect examples.
The Jetpack Security (JetSec) crypto library provides abstractions for encrypting Files and SharedPreferences objects. The library promotes the use of the AndroidKeyStore while using safe and well-known cryptographic primitives. Using EncryptedFile and EncryptedSharedPreferences allows you to locally protect files that may contain sensitive data, API keys, OAuth tokens, and other types of secrets.
Why would you want to encrypt data in your app? Doesn’t Android, since 5.0, encrypt the contents of the user’s data partition by default? It certainly does, but there are some use cases where you may want an extra level of protection. If your app uses shared storage, you should encrypt the data. In the app home directory, your app should encrypt data if your app handles sensitive information including but not limited to personally identifiable information (PII), health records, financial details, or enterprise data. When possible, we recommend that you tie this information to biometrics for an extra level of protection.
Jetpack Security is based on Tink, an open-source, cross-platform security project from Google. Tink might be appropriate if you need general encryption, hybrid encryption, or something similar. Jetpack Security data structures are fully compatible with Tink.
Key Generation
Before we jump into encrypting your data, it’s important to understand how your encryption keys will be kept safe. Jetpack Security uses a master key, which encrypts all subkeys that are used for each cryptographic operation. JetSec provides a recommended default master key in the MasterKeys class. This class uses a basic AES256-GCM key which is generated and stored in the AndroidKeyStore. The AndroidKeyStore is a container which stores cryptographic keys in the TEE or StrongBox, making them hard to extract. Subkeys are stored in a configurable SharedPreferences object.
Primarily, we use the AES256_GCM_SPEC specification in Jetpack Security, which is recommended for general use cases. AES256-GCM is symmetric and generally fast on modern devices.
For apps that require more configuration, or handle very sensitive data, it’s recommended to build your KeyGenParameterSpec , choosing options that make sense for your use. Time-bound keys with BiometricPrompt can provide an extra level of protection against rooted or compromised devices.
- userAuthenticationRequired() and userAuthenticationValiditySeconds() can be used to create a time-bound key. Time-bound keys require authorization using BiometricPrompt for both encryption and decryption of symmetric keys.
- unlockedDeviceRequired() sets a flag that helps ensure key access cannot happen if the device is not unlocked. This flag is available on Android Pie and higher.
- Use setIsStrongBoxBacked() , to run crypto operations on a stronger separate chip. This has a slight performance impact, but is more secure. It’s available on some devices that run Android Pie or higher.
Note: If your app needs to encrypt data in the background, you should not use time-bound keys or require that the device is unlocked, as you will not be able to accomplish this without a user present.
Unlocking time-bound keys
You must use BiometricPrompt to authorize the device if your key was created with the following options:
- userAuthenticationRequired is true
- userAuthenticationValiditySeconds > 0
After the user authenticates, the keys are unlocked for the amount of time set in the validity seconds field. The AndroidKeystore does not have an API to query key settings, so your app must keep track of these settings. You should build your BiometricPrompt instance in the onCreate() method of the activity where you present the dialog to the user.
BiometricPrompt code to unlock time-bound keys
Encrypt Files
Jetpack Security includes an EncryptedFile class, which removes the challenges of encrypting file data. Similar to File , EncryptedFile provides a FileInputStream object for reading and a FileOutputStream object for writing. Files are encrypted using Streaming AEAD, which follows the OAE2 definition. The data is divided into chunks and encrypted using AES256-GCM in such a way that it’s not possible to reorder.
Encrypt SharedPreferences
If your application needs to save Key-value pairs — such as API keys — JetSec provides the EncryptedSharedPreferences class, which uses the same SharedPreferences interface that you’re used to.
Both keys and values are encrypted. Keys are encrypted using AES256-SIV-CMAC, which provides a deterministic cipher text; values are encrypted with AES256-GCM and are bound to the encrypted key. This scheme allows the key data to be encrypted safely, while still allowing lookups.
More Resources
FileLocker is a sample app on the Android Security GitHub samples page. It’s a great example of how to use File encryption using Jetpack Security.
For the latest developments, please check back here. For questions, feel free to reach out to me (@jonmarkoff) on Twitter.
Источник
How to encrypt your Android device
There’s little doubt that keeping your personal data secure these days is pretty important, so it is fortunate that Android gives you the tools you need to secure your device right out of the box. If you have been wondering how to get started, this guide will walk you through how to encrypt your Android device.
What is device encryption and what does it do?
Before we go through how to enable it, it is probably best to understand what exactly encryption is and what the pros and cons are.
Device encryption is not a one-stop solution for protecting all of your data and information from prying eyes, especially when you are sending data over the internet. Instead, device encryption converts all of the data stored on your phone into a form that can only be read with the correct credentials. This goes above and beyond a regular lock screen password, as data can still be accessed from behind this screen with some specialized knowledge and use of recoveries, bootloaders, or the Android Debug Bridge.
Once encrypted, your music, photos, apps, and account data can’t be read without first unjumbling the information using a unique key. There’s a fair bit of stuff going on behind the scenes, where a user password is converted into a key that is stored in a “Trusted Execution Environment” to keep it secure from software attacks. This key is then required to encrypt and decrypt files, sort of like those alphabet cypher puzzles that scramble up letters.
With Android, this is very simple from a user’s viewpoint. You just enter your passcode whenever you boot up or unlock the device and all of your files will be accessible. This means that if your handset falls into the wrong hands, no-one else will be able to make sense of any of the data on your phone without knowing your password.
Before you leap in, there are a couple of points to consider. Firstly, opening up encrypted files requires additional processing power, so this will take a slight toll on the performance of your handset. Memory reading speeds can be a lot slower on older devices, but the performance hit in the vast majority of regular tasks is only very minor, if even noticeable at all.
Secondly, only some smartphones will offer an option to remove encryption from your handset. Encryption is a one way only process for most smartphones and tablets. If your handset doesn’t offer an option to decrypt the entire phone, the only option is to perform a complete factory reset that removed all of your personal data from the device. So check this out with your manufacturer beforehand.
With that out of the way, let’s explore how to turn encryption on.
How to encrypt my Android device?
Device encryption works in the much the same way across all Android devices, but the methods for enabling it have changed ever so slightly over the years. Most devices come with encryption enabled by default these days, particularly those running newer versions of Android. If your phone doesn’t have it enabled, you can do it manually with just a few taps.
Android 5.0 or higher
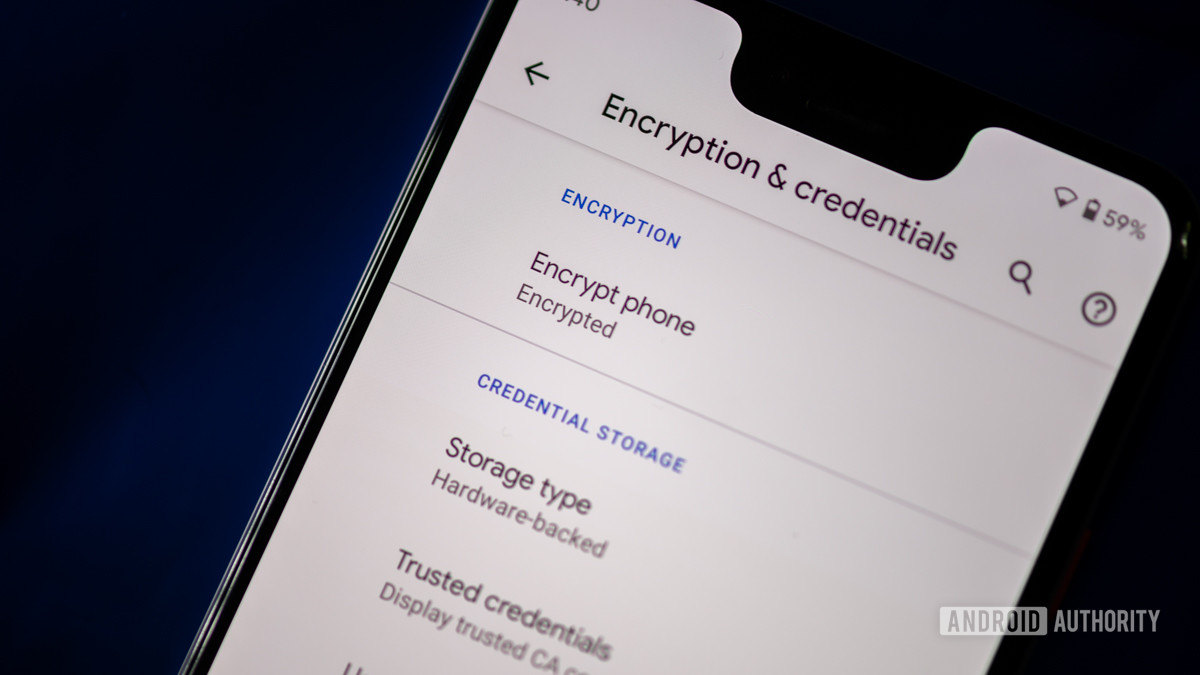
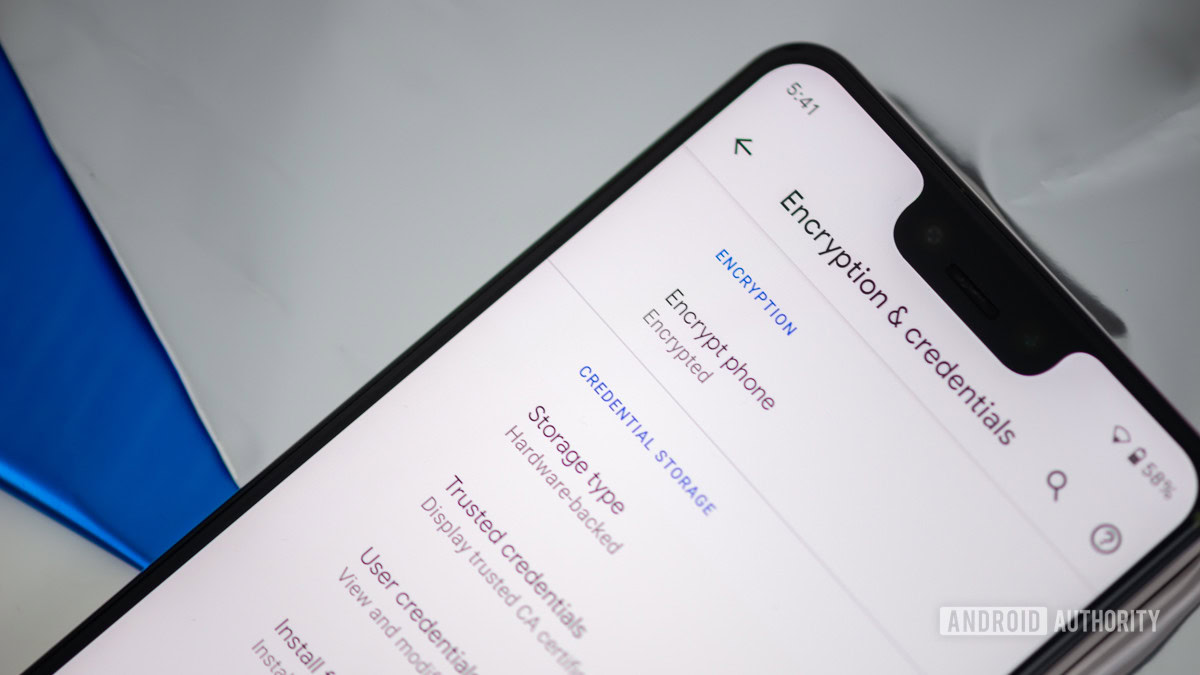
For Android handsets and tablets running Android 5.0 Lollipop or newer, you can navigate straight to the “Security” menu under settings. Getting here might be slightly different depending on your OEM, but with stock Android, this can be found under Settings > Personal > Security.
Here you should see an option to “Encrypt phone” or “Encrypt tablet”. You’ll be asked to plug your phone in to charge while the process takes place, just to make sure that your phone doesn’t shut off and cause errors. If you haven’t done so already, you will be prompted to set a lock screen PIN or password, which you will need to enter when you turn your phone on or unlock it in order to access your newly encrypted files. Be sure to remember this password!
Android 4.4 or lower
If you’re running a handset with Android 4.4 KitKat or lower, you will have to set up a PIN or password before starting up the encryption process. Fortunately, this is simple enough. Head on over to Settings > Security > Screen Lock and either pick a pattern, numbered PIN, or mixed password for your lock screen. This will be the same password used after encryption, so make a note of it.
Once that’s done, you can go back to the Security menu and hit “Encrypt phone” or “Encrypt tablet.” You’ll need to have your phone plugged in and read through the warning messages, and you will almost certainly have to confirm your PIN or password one last time before the encryption process starts.
Encrypting your phone can take an hour or more, depending on how powerful your handset is and the amount of data that you have saved on the device. Once the process is finally finished, you can enter your PIN and start using your newly encrypted device.
Back in the Security menu, you will also likely spot an option to encrypt files on your microSD card as well. This is a recommended step if you want to keep all of your data secure, but it isn’t really necessary if you’re just using your microSD card to save music or films that aren’t particularly personal.
There are a few caveats here too. Firstly, you will no longer be able to use your microSD card with other devices without completely removing the encryption first, as other phones or computers won’t know the key. Although an encrypted microSD card is still completely transparent to move files to and from over USB, just so long as you access the encrypted files from the phone used to encrypt it. Furthermore, if you reset your device before selecting decrypt, then the encryption key will be lost and you won’t be able to gain access to the secure files on your microSD card. So think about this one carefully.
And you’re done
That’s it. It really is that simple to encrypt Android devices and is a great way to keep your data a lot more secure. There are minimal trade-offs in terms of performance, but any differences should be very hard to notice on modern handsets.
Extra options with third-party apps
If you don’t fancy committing yourself to full device encryption, there are a small number of Encrypt Android apps in the Play Store that offer up a section of different features, including single file, text, and folder encryption options.
SSE – Universal Encryption App
The app also features a text encryptor and a password vault. The text editor can be used for keeping encrypted notes and these can be shared across platforms. The vault is designed to store and manage all of your passwords, PINs, and notes in one secure place protected by one master password. Sort of like an encrypted LastPass on your device.
Crypto Ghost – File Encryption
It’s not possible to encrypt files to share using the default Android method, as they are decrypted on the device first and you can’t reproduce keys for use on other devices. So this is a handy solution for sharing files that you might not want others to see.
Safe Camera – Photo Encryption
Once you’ve taken your pictures, you can share them using your master password for the app, a unique password, or even decrypt them if you want to. There’s an option to import and secure existing photos, and the app also supports GIFs.
Speaking of communication, there are also a number of apps that offer encrypted communications over both the web and text. Although these apps require you to set-up and share keys with your partners, so there’s a fair bit more work involved here.
New Android security and encryption features
As mentioned, most new Android smartphones have device encryption turned on automatically. A big change that was introduced a couple of years ago with Android 7.0 Nougat was Direct Boot. Before Direct Boot, your entire encrypted phone would be locked down until you enter the password. Since Nougat, the system allows a small selection of software to run as soon as you turn on your phone. This means that phone calls, alarms, and the like can right away from boot, while apps that you download and more personal data won’t work until you enter the password.
This was a part of Google’s revised approach to encryption, which saw the old entire partition encryption method replaced by file-level encryption. File-level encryption is faster on older devices because the system doesn’t have to decrypt huge chunks of data all at once. This method has the added benefit of granting apps much finer control over the data that is and isn’t decrypted, which can significantly improve security in the event that a system is compromised.
Google continued to further improve its security features with Android 8.0 Oreo with more granular control over app permissions, additions to the Verified Boot feature, native two-factor authentication support, and more. More importantly, Oreo also introduced enhanced encryption for the enterprise. All devices are able to utilize separate encryption keys for personal and work profiles. Device administrators are also given the ability to activate work profile keys remotely to ensure complete data protection. Oreo also brought Project Treble with it, which was another big step to ensure faster delivery of software and security updates.
Android 9.0 Pie introduced some key privacy and encryption features as well. Apps running in the background no longer have access to the mic and camera and other sensors (other than GPS). Also huge is the addition of client-side encryption.
While all data backed up from your Android device to Google’s servers is encrypted, it is encrypted by Google for Google. In other words, Google can still technically access it. With Android Pie, backups are encrypted with a client-side secret. As before, your data travels over a secure, encrypted connection to Google’s servers, but the actual data is encrypted using a password that only you know. This also means your PIN, pattern, or password is required to restore data from the backups.
With Android 10, Google took things a step further. All phones running the latest version of Android have to be encrypted by default, including entry-level devices. These were previously exempt since they lack the hardware required for advanced encryption. Not anymore. With Android 10, Google introduced Adiantum, which is a new method of encryption that works on the most budget of budget phones (including Android Go phones) and can even work on things like smartwatches and smart TVs.
Android 10 also adopts TLS 1.3, which encrypts and secures the traffic from your phone to whatever internet-based service you are connecting to. In other words, that purchase you want to make while surfing the Wi-Fi at Starbucks is now forcibly protected.
Additionally, Google introduced several other privacy features with Android 10. You no longer have to give an app full permission to things like location and microphone. Instead, you can give the app permission to use that stuff only while it’s active. Apps can also no longer access device information like the serial and IMEI number.
Given the amount of sensitive personal information that we keep on our mobile devices these days, including banking details, encrypting your Android device is a very sensible decision. There are quite a few options out there offering various levels of security, from system-wide Android encryption to apps dedicated to protecting more specific files. Keep in mind though, encryption won’t give you complete protection from everything, but it offers excellent protection in the case of stolen devices.
Источник